Routing policies and BGP communities
For a public AWS Direct Connect connection, AWS Direct Connect uses incoming (from your on-premises data center) and outgoing (from your AWS Region) routing policies.
The following inbound routing policies apply:
- The public prefixes must be owned by the user and registered in the appropriate regional internet registration.
- We must direct traffic to Amazon public prefixes. Transitive routing is not supported.
-
AWS Direct Connect uses inbound packet filtering to ensure that the traffic came from the advertised prefix.
The following outbound routing policies apply:
- AWS Direct Connect is the recommended method for traffic sourced from Amazon, and AS-PATH and Longest Prefix Match are utilised to establish the routing path.
- AWS Direct Connect advertises all local and remote AWS Region prefixes and includes on-net prefixes from other AWS non-Region points of presence (PoP), for example, CloudFront and Route 53.
- AWS Direct Connect advertises prefixes with a minimum path length of 3.
- AWS Direct Connect advertises all public prefixes with the well-known NO_EXPORT BGP community.
- If you have multiple AWS Direct Connect connections, you can adjust the load-sharing of inbound traffic by advertising prefixes with similar path attributes.
- The prefixes advertised by AWS Direct Connect must not be advertised beyond the network boundaries of your connection. For example, We must not include these prefixes in any public internet routing table.
-
AWS Direct Connect keeps prefixes advertised by customers within the Amazon network. We do not re-advertise customer prefixes learned from a public VIF to any of the following:
- Other AWS Direct Connect customers
- Networks that peer with the AWS Global Network
-
Amazon's transit providers
A Person can apply BGP community tags on the public prefixes that he advertises to Amazon to indicate how far to propagate his prefixes in the Amazon network, for the local AWS Region only, all Regions within a continent, or all public Regions.
We can use the following BGP communities for adding prefixes:
- 7224:9100—Local AWS Region
-
7224:9200—All AWS Regions for a continent
- North America–wide
- Asia Pacific
- Europe, the Middle East and Africa
-
7224:9300—Global (all public AWS Regions)
After finishing off with the discussion of AWS routing policies and BGP communities, we move to another part which will be virtual interface routing examples.
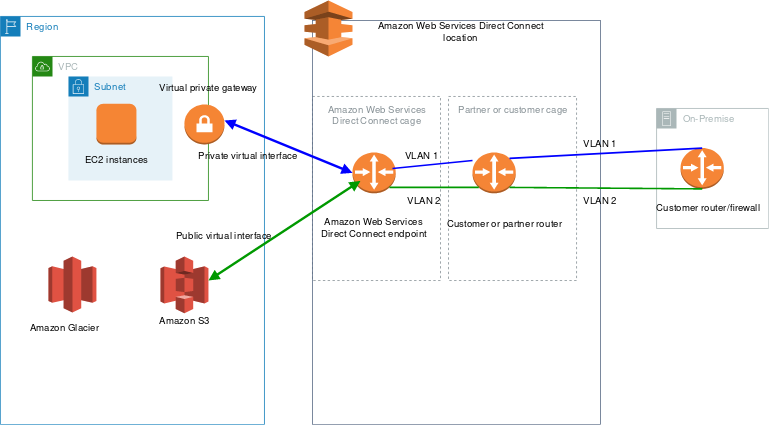
Private virtual interface routing example
Consider the case when the AWS Direct Connect location 1 home Region (east) and the VPC home Region are the same. There is a redundant AWS Direct Connect location 2 in a separate Region(west). From AWS Direct Connect location 1 to the Direct Connect gateway, there are two private VIFs. From AWS Direct Connect location 2 to the Direct Connect gateway, there is only one private VIF. Set the AS_PATH property of VIF B to be shorter than the AS_PATH attribute of VIF A to have AWS send traffic across VIF B before VIF A.

Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/private-transit-vif-example.html
The VIFs have the following configurations:
- VIP A (in us-east-1) advertises 172.16.0.0/16 and has an AS_PATH attribute of 65001, 65001, 65001
- VIF B (in us-east-1) advertises 172.16.0.0/16 and has an AS_PATH attribute of 65001, 65001
- VIF C (in us-west-1) advertises 172.16.0.0/16 and has an AS_PATH attribute of 65001
If you change the CIDR range configuration of VIF C, routes that fall into the VIF C CIDR range use VIF C because it has the longest prefix match.
- VIF C (in us-west-1) advertises 172.16.0.0/24 and has an AS_PATH attribute of 65001
The question arises of how to use the AWS direct connect resiliency to configure a maximum resiliency model, so we move to another important topic.
AWS Direct Connect Resiliency Toolkit
Some important components of AWS Direct Connect Resiliency Toolkit are:
Maximum resiliency
The following instructions show how to utilize the AWS Direct Connect Resiliency Toolkit to configure a maximum resiliency model.
1: Sign up for AWS
2: Configure the resiliency model
3: Create your virtual interfaces
4: Verify your virtual interface resiliency configuration
5: Verify your virtual interface's connectivity
High resiliency
You can achieve high resiliency for critical workloads by using two connections to multiple locations (as shown in the following figure). This type protects against connectivity failures caused by a fibre cut or a device failure. It also aids in the prevention of a complete location failure.
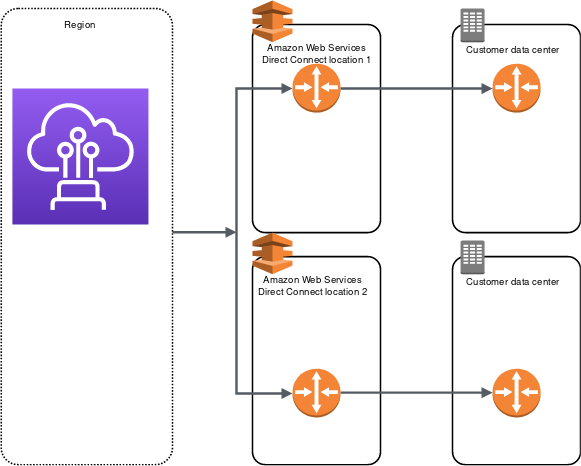
Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/images/dc-high-resiliency.png
As development and test models are one of the main hot topics to be talked about in the AWS Direct connect, we will study them in detail in the following lines.
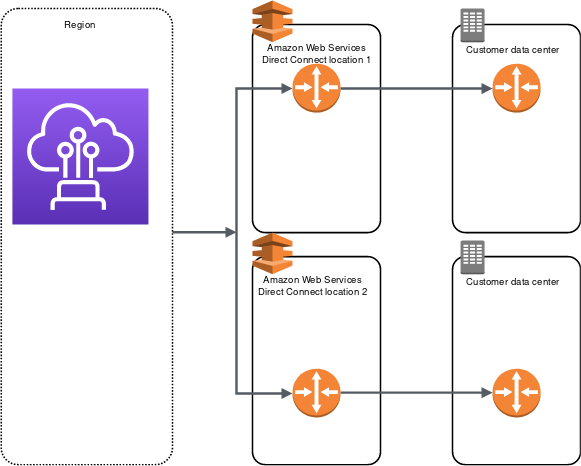
Development and test
For non-critical workloads, you may develop and test resilience by leveraging distinct connections that terminate on separate devices (as shown in the following figure). This paradigm is resilient against device failure but not against location failure.
 Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/dev-test-resiliency.html
Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/dev-test-resiliency.html
Classic
The following procedures demonstrate the common scenarios for getting set up with an AWS Direct Connect connection.
We require a single-mode fibre with a 1000BASE-LX (1310 nm) transceiver for 1 gigabit Ethernet and a 10GBASE-LR (1310 nm) transceiver for 10 gigabits or a 100GBASE-LR4 for 100 gigabit Ethernet.
1: Sign up for AWS
2: Request an AWS Direct Connect dedicated connection or accept a hosted connection
3:(Dedicated connection) Download the LOA-CFA
4: Create a virtual interface
5: Download the router configuration
6: Verify your virtual interface
7: Configure redundant connections (Recommended)
AWS Direct Connect Failover Test
The resilience models in the AWS Direct Connect Resiliency Toolkit are intended to guarantee that you have many virtual interface connections in various locations.
AWS deletes the test history after a year. The history contains information such as which AWS tested BGP peering sessions, the start and finish timings, and the test status, which can be any of the values listed below:
- In progress - The test is currently running.
- Completed - The test ran for the time that you specified.
- Canceled - We canceled the test before the specified time.
- Failed - The test did not run for the time that you specified. This can happen when there is an issue with the router.
Security is one of the issues of the main concerns concerning the developers' perspective and the operator's perspective, so now we move on to another section of MAC security.
MAC Security
An IEEE standard provides data confidentiality, data integrity, and data origin authenticity to the network.
The following are the major MACsec concepts:
- MAC Security (MACsec) — It is An IEEE 802.1 Layer 2 standard that ensures data secrecy, integrity, and authenticity of origin. We may find more information about the protocol here.
- MACsec secret key is A pre-shared key that establishes the MACsec connectivity between the customer's on-premises router and the connection port at the AWS Direct Connect location.
- Connection Key Name (CKN) and Connectivity Association Key (CAK) — The values in this pair are used to generate the MACsec secret key. You generate the pair values, associate them with an AWS Direct Connect connection, and provision them on your edge device at your end.
AWS Direct Connect connections
AWS Direct Connect allows you to create a dedicated network link between your network and AWS Direct Connect facilities.
The following are two types of connections:
- Dedicated Connection: A physical Ethernet connection associated with a single customer. Customers can request a dedicated connection using the AWS Direct Connect Console, the command-line interface(CLI), or the API.
- Hosted Connection: A physical Ethernet connection that an AWS Direct Connect Partner provisions on behalf of a customer. Customers request a hosted connection by contacting a partner in the AWS Direct Connect Partner Program, who provides the connection.
AWS Direct Connect virtual interfaces
A User must create one of the following virtual interfaces to begin using his AWS Direct Connect connection.
- Private virtual interface: A private virtual interface should access an Amazon VPC using private IP addresses.
- Public virtual interface: A virtual public interface can access all AWS public services using public IP addresses.
- Transit virtual interface: A transit virtual interface should access one or more Amazon VPC Transit Gateways associated with Direct Connect gateways. You can use virtual transit interfaces with 1/2/5/10 Gbps AWS Direct Connect connections. For information about Direct Connect gateway configurations.
Security in AWS Direct Connect
Security is a mutual responsibility between AWS and the individual. The shared responsibility model describes this by the security of the Cloud and security in the Cloud.
- Security of the Cloud – It is responsible for protecting the infrastructure that runs the services in AWS Cloud. It provides services that are purely secure to use. Also, third-party auditors keep verifying and testing the effectiveness of security of the Cloud at regular intervals.
- Security in the Cloud – Our responsibility is determined by the AWS service we use. We are also responsible for other factors, including the sensitivity of your data, your company's requirements, and applicable laws and regulations.
Data protection in AWS Direct Connect
We can secure our data in the following ways.
- We can use multi-factor authentication (MFA) with each account.
- We can use SSL/TLS to communicate with AWS resources. We recommend TLS 1.2 or later.
- Set up API and user activity logging with AWS CloudTrail.
- Use AWS encryption solutions and all default security controls within AWS services.
- Use Amazon Macie or other advanced managed security services, which assist in discovering and securing personal data that is stored in Amazon S3.
- We can use the FIPS endpoint if one requires FIPS 140-2 validated cryptographic modules when accessing AWS through a command-line interface or an API.
- Let us now move to the FAQs section.
Frequently Asked Questions
What is AWS Direct Connect?
AWS Direct Connect is a networking solution that offers an option to connect to AWS over the Internet.
What is the difference between hosted and dedicated connections?
A dedicated connection is made through a 100 Gbps, 10 Gbps, or 1 Gbps Ethernet port dedicated to a single customer. Hosted connections are sourced from an AWS Direct Connect Partner.
What is MACsec?
MAC Security (MACsec) is an IEEE standard that provides data confidentiality, data integrity, and data origin authenticity.
What happens after a failover test is complete?
We reestablish the Border Gateway Protocol session between the on-premises networks and AWS after the set test length by utilizing the Border Gateway Protocol session parameters established before the test is begun.
Can I run failover tests for any type of virtual interface?
Yes, you may perform virtual interface-based Border Gateway Protocol session(s) tests.
Conclusion
In this article, we have extensively discussed AWS Direct connect. Then we have discussed Some components of the AWS Direct Connect Resiliency Toolkit. After that, we learned about MAC security, AWS DC connections, virtual interface, and all last Security in AWS Direct Connect.
In the end, we have also answered some important FAQs.
After reading about the AWS Direct connect, are you not feeling excited to read/explore more articles on the topic of AWS? Don't worry; Coding Ninjas has you covered. To learn, see Introduction to AWS, AWS Features, Managing Devices with AWS IoT, AWS Amplify, and AWS Cost & Usage Report.
Check out this problem - Longest Common Prefix
Refer to our Guided Path on Coding Ninjas Studio to upskill yourself in Data Structures and Algorithms, Competitive Programming, JavaScript, System Design, and many more! If you want to test your competency in coding, you may check out the mock test series and participate in the contests hosted on Coding Ninjas Studio! But if you have just started your learning process and are looking for questions asked by tech giants like Amazon, Microsoft, Uber, etc., you must look at the problems, interview experiences, and interview bundle for placement preparations.
Nevertheless, you may consider our paid courses to give your career an edge over others!
Do upvote our blogs if you find them helpful and engaging!
Happy Learning!




 Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/dev-test-resiliency.html
Source: https://docs.aws.amazon.com/directconnect/latest/UserGuide/dev-test-resiliency.html



