Introduction
UGC NET Exam is a very popular exam in India for people interested in research. Solving Previous Year Questions is an excellent way to learn about the exam pattern and practice it. By solving the PYQs, you will get a basic idea about your preparation. In this article, we have given the questions of UGC NET 2015 Dec Paper-III. We have also explained every problem adequately to help you learn better.
Note: This article contains Question No. 51 to Question No. 75 out of the 75 questions asked in UGC NET Dec 2015 paper III. You can find Question No 1 to Question No 25 in part-1 and Question No 26 to Question No 50 in part-2.
Question 1: Blind image deconvolution is ................
- Combination of blur identification and image restoration
- Combination of segmentation and classification
- Combination of blur and non-blur image
- None of the above
Solution : (A) Combination of blur identification and image restoration
Explanation:
The combination of blur detection and image restoration is known as blind image deconvolution.
Question 2: A basic feasible solution of a linear programming problem is said to be ............... if at least one of the basic variable is zero.
- degenerate
- Non-degenerate
- Infeasible
- Unbounded
Solution: (A) degenerated
Explanation:
If at least one of the basic variables is zero, a linear programming problem's basic viable solution is said to be degenerate.
Basic feasible solutions are feasible solutions to LP. It is of two type:
1 – Non – degenerate: If all values of the basic variable are non – zero and positive.
2 – Degenerate: If atleast one basic variable is zero.
So, option (A) is correct.
Question 3: Consider the following conditions :
(a) The solution must be feasible, i.e. it must satisfy all the supply and demand constraints.
(b) The number of positive allocations must be equal to m+n-1, where m is the number
of rows and n is the number of columns.
(c) All the positive allocations must be in independent positions.
The initial solution to a transportation problem is said to be a non-degenerate basic feasible solution if it satisfies :
Codes :
- (a) and (b) only
- (a) and (c) only
- (b) and (c) only
- (a), (b) and (c)
Solution: (D) (a), (b) and (c)
Explanation:
If a transportation problem's initial solution satisfies the following criteria, it is said to be a non-degenerate basic feasible solution: (a)The solution must be feasible, that is, it must satisfy all supply and demand constraints.
(b)The total number of positive allocations must be m1n21, where m denotes the number of rows and n denotes the number of columns.
(c)All positive allocations must be placed in separate positions.
As a result, option (D) is the correct answer.
Question 4: Consider the following transportation problem :
|
Factories |
Stores | |||||
| I | II | III | IV | Supply | ||
| A | 4 | 6 | 8 | 13 | 50 | |
| B | 13 | 11 | 10 | 8 | 70 | |
| C | 14 | 4 | 10 | 13 | 30 | |
| D | 9 | 11 | 13 | 8 | 50 | |
| Demand | 25 | 35 | 105 | 20 | ||
The transportation cost in the initial basic feasible solution of the above transportation problem using Vogel’s Approximation method is :
- 1450
- 1465
- 1480
- 1520
Solution: (B) 1465
Explanation:
B is the answer. Because demand and supply are not equal in this case, a dummy column (with cost 0 for all items) with demand 15 is inserted to help balance things out. Then, using Vogel's method, penalties are calculated, and the row with the largest penalties is chosen, and if there is a tie, the min, next min-cost, and so on are chosen.
Question 5: The character set used in Windows 2000 operating system is ...............
- 8 bit ASCII
- Extended ASCII
- 16 bit UNICODE
- 12 bit UNICODE
Solution: (C) 16 bit UNICODE
Explanation:
In the Windows 2000 operating system 16-bit UNICODE character set is used.
Extended ASCII character encodings are 8-bit or bigger encodings that include 7-bit ASCII characters as well as extra characters.
ASCII coding is an 8-bit character encoding system.
As a result, Option (C) is the correct answer.
Question 6: In Unix, the command to enable execution permission for file “mylife” by all is ................
- Chmod ugo+X myfile
- Chmod a+X myfile
- Chmod +X myfile
- All of the above
Solution: (D) All of the above
Explanation:
All the above three commands are used to enable execution permission.
Question 7: What will be the output of the following Unix command ?
$rm chap0\[1 - 3\]
- Remove file chap0[1 - 3]
- Remove file chap01, chap02, chap03
- Remove file chap\[1 - 3\]
- None of the above
Solution (A) Remove file chap0[1 - 3]
Explanation:
Square brackets can be used to surround a single character (one digit or one letter) that you want to match. [Cc]hapter, for example, might be either Chapter or Chapter, whereas [ch]apter could be either capter or hapter. To divide a group of consecutive characters, use a hyphen (-). For instance, chap[1-3] might correspond to chap1, chap2, or chap3.
However, if escape sequence(\) is used, the result is same to that after \
As a result, $rm chap0 13 will be removed.
Remove the files chap0[1-3].
Question 8: Which of the following statements regarding the features of the object-oriented approach to databases are true ?
(a) The ability to develop more realistic models of the real world.
(b) The ability to represent the world in a non-geometric way.
(c) The ability to develop databases using natural language approaches.
(d) The need to split objects into their component parts.
(e) The ability to develop database models based on location rather than state and behaviour.
Codes :
- (a), (b) and (c)
- (b), (c) and (d)
- (a), (d) and (e)
- (c), (d) and (e)
Solution: (A) (a), (b) and (c)
Explanation:
The following are characteristics of the object-oriented database approach:
The ability to create more realistic real-world models.
The ability to visualise the world in a non-geometrical manner.
The capacity to create databases with natural language techniques.
As a result, option (A) is the correct answer.
Question 9: Consider the following database table:
Create table test(
one integer,
two integers,
primary key(one),
unique(two),
check(one≥1 and ≤10),
check(two≥1 and ≤5) );
How many data records/tuples almost can this table contain?
- 5
- 10
- 15
- 50
Solution: (A) 5
Explanation:
check(one >= 1 and <= 10), check(two >= 1 and <= 5).
The number of tuples will be determined by the second constraint. Or, to put it another way, the common condition will take precedence.
i.e., check(two >= 1 and <= 5) 5 tuples.
As a result, option (A) is the correct answer.
Question 10: Suppose ORACLE relation R(A, B) currently has tuples {(1, 2), (1, 3), (3, 4)} and relation S(B, C) currently has {(2, 5), (4, 6), (7, 8)}. Consider the following two SQL queries SQ1 and SQ2:
SQ1: Select *
From R Full Join S
On R.B=S.B;
SQ2: Select *
From R Inner Join S
On R.B=S.B;
The numbers of tuples in the result of the SQL query SQ1 and the SQL query SQ2 are given by:
- 2 and 6 respectively
- 6 and 2 respectively
- 2 and 4 respectively
- 4 and 2 respectively
Solution: (D) 4 and 2 respectively
Explanation:
Full join will give two matches for B = 2 and B = 4. and two mismatches So it will give 4 output.
An inner join will give output for only matching conditions. B = 2 and B = 4. Two output from the inner join.
So, option (D) is correct.
Question 11: Consider the following three SQL queries (Assume the data in the people table) :
(a) Select Name from people where Age>21;
(b) Select Name from people where Height>180;
(c) Select Name from people where (Age>21) or (Height>180);
If the SQL queries (a) and (b) above, return 10 rows and 7 rows in the result set respectively, then what is one possible number of rows returned by the SQL query (c)?
- 3
- 7
- 10
- 21
Solution: (C)10
Explanation:
According to the question: Return 10 rows if you select a name from those who are over the age of 21.
Returns 7 rows if you select Name among people with a height more than 180.
Select Name from People where (Age > 21) or (Height > 180) returns 10 rows. Because there is a choice between the two conditions. As a result, it will return ten rows.
As a result, option (C) is the correct answer.
Question 12: The distributed system is a collection of (P) and communication is achieved in a distributed system by (Q), where (P) and (Q) are:
- Loosely coupled hardware on tightly coupled software and disk sharing, respectively.
- Tightly coupled hardware on loosely coupled software and shared memory, respectively.
- Tightly coupled software on loosely coupled hardware and message passing, respectively.
- Loosely coupled software on tightly coupled hardware and file sharing, respectively.
Solution: (C) Tightly coupled software on loosely coupled hardware and message passing respectively.
Explanation:
The distributed system is made up of (P), and communication is accomplished via (Q), where (P) and (Q) refer to tightly coupled software on loosely linked hardware and message passing, respectively.
As a result, option (C) is the correct answer.
Question 13: Consider the following three tables R, S and T. In this question, all the join operations are natural joins (⨝). (π) is the projection operation of a relation :
| R | S | T |
| A B | B C | A C |
|
1 2
3 2
5 6
7 8
9 8 |
6 2
2 4
8 1
8 3
2 5 |
7 1
1 2
9 3
5 4
3 5 |
Possible answer tables for this question are also given as below:
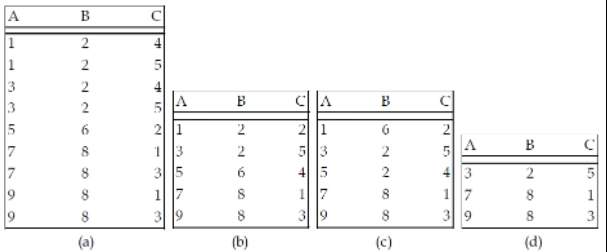
What is the resulting table of πA,B(R⨝T) ⨝ πB,C(S⨝T) ?
- (a)
- (b)
- (c)
- (d)
Solution: A (a)
Explanation:
The A) option returns all potential results following a natural join, but it does not involve the table t, hence it is false.
In the b)option, records 5 6 4 and 1 2 2 are not conceivable, hence the outcome is false.
In the c) option, After a natural join of the table, record 5 2 4 and record 1 6 2 is not feasible.
After merging all three tables, the d) option contains a partial result.
As a result, option d should be selected.
Question 14: Consider the two-class classification task that consists of the following points:
Class C1: [-1, -1], [-1, 1], [1, -1]
Class C2: [1, 1]
The decision boundary between the two classes C1 and C2 using single perceptron is given by:
- x1-x2-0.5=0
- -x1+x2-0.5=0
- 0.5(x1+x2)-1.5=0
- x1+x2-0.5=0
Solution: (D) x1+x2-0.5=0
Explanation:
It assumes a sign function, i.e try replacing x and y, the equation which classifies the dataset properly is the right answer.
e.g for case four.
-1 -1 -.5 = -2.5 since it turned out negative call it Class C1
-1+1 -.5=-.5 class C1
1-1-.5=-.5 class C1
and finally
1+1-.5-=1.5 since this is positive call it C2
Note: option D is the only equation that classifies them properly hence the answer.
Question 15: Consider a standard additive model consisting of rules of the form of
If x is Ai AND y is Bi THEN z is Ci.
Given crisp inputs x=x0, y=y0, the output of the model is :

Solution: (C)
Explanation:
The Standard Additive model (SAM) includes the centroid defuzzification technique.
Hence, z = centroid (∑iµAi, (xo) µBi, (yo) µ(iz)
Question 16: A bell-shaped membership function is specified by three parameters (a, b, c) as follows:
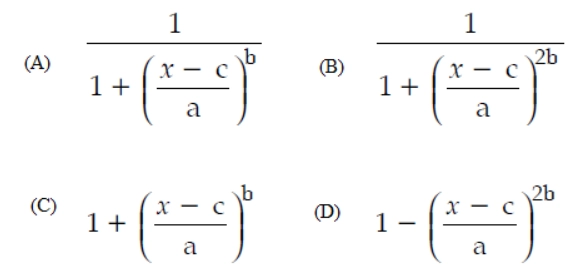
Solution: (B)
Explanation:
The generalized bell function depends on the three parameters a, b, and c is given by:
f(x, a, b, c) = (1/(1 + (|(x - c)/a|)2b))
Where the parameter b is usually positive. The parameter c locates the center of the curve. Enter the parameter vector params, the second argument for a bell membership function, as the vector whose entries are a,b and c, respectively.
Question 17: Which of the following is/are the principal components of a memory-tube display?
(a) Flooding gun (b) Collector
(c) Phosphorus grains (d) Ground
Codes:
- (a) and (b)
- (c) only
- (d) only
- All the above
Solution: (D) All the above
Explanation:
The flooding gun, collector, phosphorus grains, and ground are the main components of a memory-tube display.
As a result, option (D) is the correct answer.
Question 18: Which of the following steps is/are not required for analog to digital conversion?
(a) Sensing (b) Conversion (c) Amplification
(d) Conditioning (e) Quantization
Codes:
- (a) and (b)
- (c) and (d)
- (a), (b) and (e)
- None of the above
Solution: (D) None of the above
Explanation:
Sensing, quantization, amplification, and conversion are all required for analog to digital conversion.
Analog to digital conversion includes steps b, c, and e.
No permutation of option is correct.
As a result, option (D) is the correct answer.
Question 19: Which raster locations would be chosen by Bresenham’s algorithm when scanning a line from (1, 1) to (8, 5)?
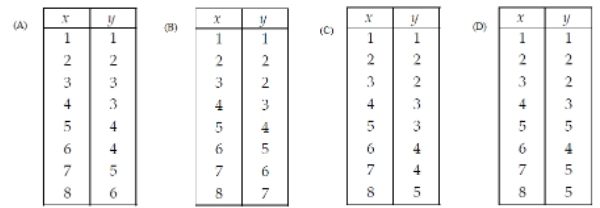
- A
- B
- C
- D
Solution: (C)
Explanation:
Option A and B are not ending at (8, 5) and in option D there is an increment of two, which is invalid. Only option C is reaching (8, 5).
Question 20: Consider a unit square centered at the origin. The coordinates of the square are translated by a factor (1/2, 1) and rotated by an angle of 90o. What shall be the coordinates of the new square?
- (-1/2, 0), (-1/2, 1), (-3/2, 1), (-3/2, 0)
- (-1/2, 0), (1/2, 1), (3/2, 1), (3/2, 0)
- (-1/2, 0), (1/2, 0), (-3/2, 1), (-3/2, 0)
- (-1/2, 0), (1/2, 1), (-3/2, 1), (-3/2, 0)
Solution: (A) (-1/2, 0), (-1/2, 1), (-3/2, 1), (-3/2, 0)
Explanation:
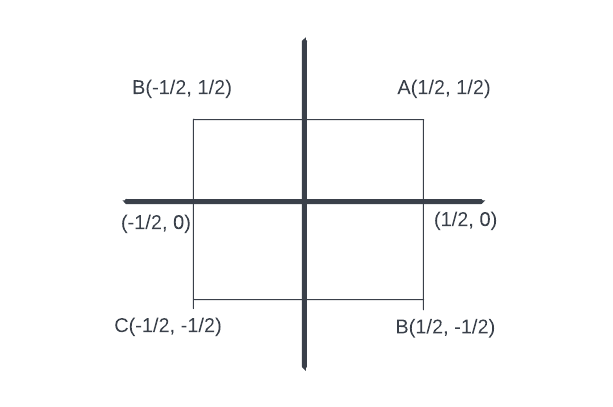
Translation is applied by a factor(½,1) to all 4 endpoints. Hence they becomes as below by using x’ = x + tx
Y’ = y + ty
Here tx=½ and ty=1
A = (1, 3/2); B = (0, 3/2), C = (0, ½ ), D = (1, ½ )
Rotation by angle 90o according to formula:
x’ = xcos(90o) -y sin(90o); y’ = xsin(90o) + ycos(90o)
For A: x’ = -3/2, y =1 → A’(-3/2, 1)
B: x’ = -3/2, y = 0, So; B’ = (-3/2,0)
C: x’ = -½, y’ = 0; So, C’ = (-½, 0)
D: x’ = -½, y’ = 1; So, D’ = (-½, 1)
Question 21: Which of the following is/are the components of a CRT ?
(a) Electron Gun
(b) Control Electrode
(c) Focusing Electrode
(d) Phosphor Coated Screen
Codes :
- (a) and (d)
- (a), (b) and (d)
- (a), (b), (c) and (d)
- (a), (c) and (d)
Solution: (C) (a), (b), (c) and (d)
Explanation:
Components of a CRT are:
(a)Electron Gun
(b)Control Electrode
(c)Focusing Electrode
(d)Phosphor Coated Screen
So, option (C) is correct.
Question 22: Which one of the following statements is incorrect?
- Pareto analysis is a statistical method used for analyzing causes and is one of the primary tools for quality management.
- Reliability of a software specifies the probability of failure-free operation of that software for a given time duration.
- The reliability of a system can also be specified as the Mean Time To Failure (MTTF).
- In white-box testing, the test cases are decided on the specifications or the requirements.
Solution: (D) In white-box testing, the test cases are decided from the specifications or the requirements.
Explanation:
The design phase of the software development lifecycle yields test cases for white box testing. White box testing uses data flow testing, control flow testing, path testing, branch testing, statement, and decision coverage as a guideline to produce error-free software.
Question 23: Consider a language A defined over the alphabet ∑={0, 1} as A = {0[n/2] 1n: n >= 0} .
The expression [n/2] means the floor of n/2, or what you get by rounding n/2 down to the nearest integer.
Which of the following is not an example of a string in A ?
- 011
- 01111
- 0011
- 001111
Solution: (C) 0011
Explanation:
If n=2
[n/2] = [1] = 1 i.e. Language is : 011
if n=3
[n/2] = [1.5] = 1 i.e. Language is : 0111
if n=4
[n/2] = [2] = 2 i.e. Language is : 001111
Hence option A is possible, B is possible, D is possible but C is not possible.
Question 24: Which one of the following statements, related to the requirements phase in Software Engineering, is incorrect?
- “Requirement validation” is one of the activities in the requirements phase.
- “Prototyping” is one of the methods for requirement analysis.
- “Modelling-oriented approach” is one of the methods for specifying the functional specifications.
- “Function points” is one of the most commonly used size metrics for requirements.
Solution: (C) “Modelling-oriented approach” is one of the methods for specifying the functional specifications.
Explanation:
One of the activities in the requirements phase is "requirement validation." One of the strategies for requirement analysis is correct "prototyping." One of the approaches for providing functional specifications is to use a correct "modeling-oriented approach." One of the most widely utilised size metrics for requirements is incorrect "Function points." Correct
As a result, option (C) is the correct answer.
Question 25: ............... tag is an extension to HTML that can enclose any number of Javascript statements.
- <SCRIPT>
- <BODY>
- <HEAD>
- <TITLE>
Answer: (A) <SCRIPT>
Explanation:
<script>
document.getElementById("demo").innerHTML = "Hello JavaScript!";
</script>
FAQs
What is the UGC NET exam?
UGC NET is a national-level exam organized by UGC to determine the eligibility of the candidates for lectureship and JRF.
What is the exam format for the UGC NET?
The UGC NET exam is conducted entirely online.
Is it possible to take the UGC NET after completing a postgraduate degree?
You are qualified to take the exam if you have finished a PG Diploma from a recognized university.
How can solving PYQs help in my exam preparation?
Solving PYQs will give you a good idea about the exam pattern and help you identify your weak topics to prepare them better for the examination.
How many papers are there in the UGC NET exam?
There are two papers, and the candidates get 3 hours for both papers. There are 150 questions in UGC NET combining both papers.





