Introduction
In India, the UGC NET Exam is a very popular exam for people who want to pursue a career in research. Previous Year Questions are a great way to get a feel for the exam format. You will gain a fundamental understanding of your preparedness by completing the PYQs. You can assess your weak areas and practice on them to improve your exam performance. We have included the UGC NET 2017 January Paper-III first 25 questions in this blog. We've also thoroughly detailed each problem to aid your learning. You can get the next 25 questions in the next article Jan 2017 Paper III - Part 2
Question 1 to 25
1. Which of the following is an interrupt according to a temporal relationship with the system clock?
(1) Maskable interrupt
(2) Periodic interrupt
(3) Division by zero
(4) Synchronous interrupt
Answer: 4
Explanation:
We categorise interrupts in two ways based on their temporal relationship with the system clock:
1- Synchronous: Synchronous interrupts occur when the source of the interrupt is in phase with the system clock. To put it another way, interrupts that are timed by the system clock. Example: timer service that uses the system clock.
2- Asynchronous: Asynchronous interruptions are defined as interrupts that are not in phase with the system clock.
2. Which of the following is incorrect for virtual memory?
(1) Large programs can be written
(2) More I/O is required
(3) More addressable memory available
(4) Faster and easy swapping of process
Answer: 2
Explanation:
- When we have memory expansion, we can develop big programs.
- Virtual memory has fewer I/O requirements.
- Virtual memory provides more addressable memory.
-
Page replacement strategy in virtual memory allows for faster and easier process shifting.
3. The general configuration of the microprogrammed control unit is given below:
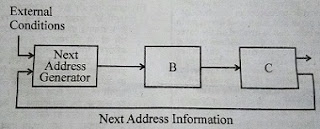
What are blocks B and C in the diagram respectively?
(1) Block address register and cache memory
(2) Control address register and control memory
(3) Branch register and cache memory
(4) Control address register and random access memory
Answer: 2
Explanation:
The logic of the control unit is specified by a micro-program. A micro-program is also called firmware (midway between the hardware and the software). It consists of:
(a) One or more micro-operations to be executed; and
(b) The information about the micro-instruction to be executed next.
Also read, microprogrammed control unit
4. Match the following:
Addressing Mode Location of operand
a. Implied i. Registers which are in CPU
b. Immediate ii. Register specifies the address
of the operand
c. Register iii. Specified in the register
d. Register Indirect iv. Specified implicitly in the
definition of instruction
Codes:
a b c d
(1) iv iii i ii
(2) iv i iii ii
(3) iv ii i iii
(4) iv iii ii i
Answer: 1
Explanation:
- The location of the operand is supplied implicitly in the specification of the instruction in Implied Addressing Mode.
- In Immediate Addressing Mode, the operand's location in the register is defined.
- In Register Addressing Mode, the operand's placement in CPU registers is determined.
- The address of the operand is specified in the Register Indirect Addressing Mode register.
5. In the 8085 microprocessor, the digit 5 indicates that the microprocessor needs
(1) -5 volts, +5 volts supply
(2) +5 volts supply only
(3) -5 volts supply only
(4) 5 MHz clock
Answer: 2
Explanation:
In 8085 microprocessor, the digit 5 indicates that the microprocessor needs +5 volts supply only.
6. In 8085, which of the following performs: load register pair immediate operation?
(1) LDAX rp
(2) LHLD addr
(3) LXI rp, data
(4) INX rp
Answer: 3
Explanation:
LXI stands for load register pair instantaneous, and it takes one register and two bytes of immediate data as input. A(accumulator), B, C, D, E, H, L, and SP, PC, flags are the seven internal 8-bit registers.
This is typically used to load a memory pointer, or SP (commonly used H-L pair in 8085). H-L, D-E, and B-C register pairings are commonly utilised. The MSB is held by B, D, and H, whereas the LSB is held by L, E, and C.
For example, LXI H, F800H loads an H-L pair with the value F800. F8 is kept in H, whereas 00 is kept in L.
7. Consider following schedules involving two transactions:
S1: r1(X); r1(Y); r2(X); r2(Y); w2(Y); w1(X)
S2: r1(X); r2(X); r2(Y); w2(Y); r1(Y); w1(X)
Which of the following statement is true?
(1) Both S1 and S2 are conflict serializable.
(2) S1 is conflict serializable and S2 is not conflict serializable.
(3) S1 is not conflict serializable and S2 is conflict serializable.
(4) Both S1 and S2 are not conflict serializable.
Answer: 3
Explanation:
S1: There are two conflicting operations here: r1(y)->w2(y) and r2(x)->w1(x), therefore there will be an edge from T1 to T2 and T2 to T1...so the graph will have a loop! As a result, it is not serializable.
S2:However, no such loops appear in the graph for any of the edges. As a result, it is possible to serialise disagreement.
|
S1 is not conflicted serializable, but S2 is conflict serializable
Schedule S1 T1 T2 --------------------- r1(X) r1(Y) r2(X) r2(Y) w2(Y) w1(X) The schedule is neither conflict equivalent to T1T2, nor T2T1.
Schedule S2 T1 T2 --------------------- r1(X) r2(X) r2(Y) w2(Y) r1(Y) w1(X) The schedule is conflict equivalent to T2T1.
|
8. Which one is correct w.r.t. RDBMS?
(1) primary key ⊆ super key ⊆ candidate key
(2) primary key ⊆ candidate key ⊆ super key
(3) super key ⊆ candidate key ⊆ primary key
(4) super key ⊆ primary key ⊆ candidate key
Answer: 2
Explanation:
primary key ⊆ candidate key ⊆ super key in RDBMS.
9. Let pk(R) denotes primary key of relation R. A many-to-one relationship that exists between two relations R1 and R2 can be expressed as follows:
(1) pk(R2)→pk(R1)
(2) pk(R1)→pk(R2)
(3) pk(R2)→R1∩R2
(4) pk(R1)→R1∩R2
Answer: 2
Explanation:
Consider the following case
A many-to-one relationship set exists between entity sets students and course (a relation r with primary key roll_no )
Let it is decomposed in 2 relations r1(student with Pk roll_no ) and r2 (course with Pk course name )
Roll_no can uniquely identify course name but course name can not uniquely identify roll_no.
So the functional dependency Pk(student) → Pk(course) indicates a many-to-one relationship between r1 and r2.
10. For a database relation R(A,B,C,D) where the domains of A,B,C and D include only atomic values, only the following functional dependencies and those that can be inferred from them are:
A→C
B→D
The relation R is in ................
(1) First normal form but not in second normal form
(2) Both in first normal form as well as in second normal form
(3) Second normal form but not in third normal form
(4) Both in second normal form as well as in third normal form
Answer: 1
Explanation:
A relation is in first normal form if every attribute in that relation is single valued attribute. It is in 1NF.
{A,B} are prime attributes and {C,D} are non-prime attribute.
A+ = {A,C}
B+ = {B,D}
{A,B}+ = {A,B,C,D} so AB is the key.
But A+ = {A,C}
B+ = {B,D} makes it a partial dependency.
So, this relation is not in 2NF.
11. Consider the following relation:
| Works (emp_name, company_name, salary) |
Here, emp_name is the primary key.
Consider the following SQL query:
|
Select emp_name From Works T where salary > (Select avg (salary) from Works S where T.company_name=S. Company_name) |
The above query is for the following:
(1) Find the highest paid employee who earns more than the average salary of all employees of his company.
(2) Find the highest paid employee who earns more than the average salary of all the employees of all the companies.
(3) Find all employees who earn more than the average salary of all employees of all the companies.
(4) Find all employees who earn more than the average salary of all employees of their company.
Answer: 4
Explanation:
Given, schema and SQL query:
| Works (emp_name, company_name, salary) |
Here, emp_name is primary key.
|
Select emp_name From works T where salary > (select avg (salary) from works S where T.company _ name = S.company _ name) |
Inner Query will calculate the company's average wage and compare it to the salaries of selected personnel. As a result, all employees who earn more than the average income of all employees at their organisation come out on top..
12. If following sequence of keys are inserted in a B+ tree with K(=3) pointers:
8, 5, 1, 7, 3, 12, 9, 6
Which of the following shall be the correct B+ tree?
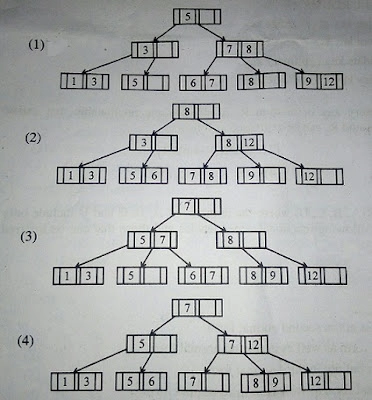
Answer: 1
Explanation:
B+ is either left-biased (<=) or it is right-biased (>=), all trees except (1) are violating the biasing property.
13. Which of the following statement(s) is/are correct?
(1) Persistence is the term used to describe the duration of phosphorescence.
(2) The control electrode is used to turn the electron beam on and off.
(3) The electron gun creates a source of electrons which are focussed into a narrow beam directed at the face of CRT.
(4) All of the above.
Answer: 4
Explanation:
- The term "persistence" is used to define how long phosphorescence lasts.
- The control electrode is used to turn on and off the electron beam.
- The electron gun provides an electron source that is focussed into a narrow beam that is directed towards the CRT's face.
Hence, All of the statements are true.
14. A segment is any object described by GKS commands and data that start with CREATE SEGMENT and Terminates with CLOSE SEGMENT command. What functions can be performed on these segments?
(1) Translation and Rotation
(2) Panning and Zooming
(3) Scaling and Shearing
(4) Translation, Rotation, Panning and Zooming
Answer: 4
Explanation:
Segments allows objects to be manipulated by referring segment number and as a result we can rotate, translate the pan and zoom it.
15. Match the following:
a. Glass i. Contains liquid crystal and serves
as a bonding surface for a conductive
coating.
b. Conductive coating ii. Acts as a conductor so that a voltage
can be applied across the liquid crystal.
c. Liquid Crystal iii. A substance which will polarize light
when a voltage is applied to it.
d. Polarized film iv. A transparent sheet that polarizes light.
Codes:
a b c d
(1) i ii iii iv
(2) i iii ii iv
(3) iv iii ii i
(4) iv ii i iii
Answer: 1
Explanation:
- Glass includes liquid crystal and serves as a conductive coating's bonding surface.
- A voltage can be placed across the liquid crystal since the conductive layer functions as a conductor.
- When a voltage is supplied to a liquid crystal, it causes light to polarise.
-
A transparent sheet that polarises light is known as polarised film.
16. Below are the few steps given for scan-converting a circle using Bresenham's Algorithm. Which of the given steps is not correct?
(1) Compute d = 3 – 2r (where r is radius)
(2) Stop if x > y
(3) If d<0, then d=4x+6 and x=x+1
(4) If d≥0,then d=4 *(x-y)+10, x=x+1 and y=y+1
Answer: 4
Explanation:
Algorithm
Step 1 − Get the coordinates of the center of the circle and radius, and store them in x, y, and R respectively. Set P=0 and Q=R.
Step 2 − Set decision parameter D = 3 – 2R.
Step 3 − Repeat through step-8 while X < Y.
Step 4 − Call Draw Circle (X, Y, P, Q).
Step 5 − Increment the value of P.
Step 6 − If D < 0 then D = D + 4x + 6.
Step 7 − Else Set Y = Y + 1, D = D + 4(X-Y) + 10.
Step 8 − Call Draw Circle (X, Y, P, Q).
17. Which of the following is/are side effects of scan conversion?
a. Aliasing
b. Unequal intensity of diagonal lines
c. Over striking in photographic applications
d. Local or Global aliasing
(1) a and b
(2) a, b and c
(3) a, c and d
(4) a, b, c and d
Answer: 4
Explanation:
Side effect of scan conversion:
1. Aliasing
2. Unequal intensity of diagonal lines
3. Over striking in photographic applications
4. Local or Global aliasing
All option are correct.
18. Consider a line AB with A = (0,0) and B = (8, 4). Apply a simple DDA algorithm and compute the first four plots on this line.
(1) [(0, 0), (1, 1), (2, 1), (3, 2)]
(2) [(0, 0), (1, 1.5), (2, 2), (3, 3)]
(3) [(0, 0), (1, 1), (2, 2.5), (3, 3)]
(4) [(0, 0), (1, 2), (2, 2), (3, 2)]
Answer: 1
Explanation:
According to DDA algorithm,
|dx| = 8, |dy| = 4
since |dx| > |dy|, steps = |dx| = 8
Xinc = |dx|/steps = 1, Yinc = |dy|/steps = 0.5.
Algorithm:
for k = 1 to steps:
Xk+1 = Yk + Xinc
Yk+1 = Yk + Yinc
// plot round(Xk+1), round(Yk+1)
Since DDA works with integer values only, we need to round the values of coordinates to nearest integer. Consider 0.5 to be rounded to 1.
Thus following the algorithm, we get the first four points as (0, 0), (1, 1), (2, 1), (3, 2).
Hence option 1 is correct.
19. Which of the following are not regular?
(A) Strings of even number of a’s.
(B) Strings of a’s, whose length is a prime number.
(C) Set of all palindromes made up of a’s and b’s.
(D) Strings of a’s whose length is a perfect square.
(1) (A) and (B) only
(2) (A), (B) and (C) only
(3) (B), (C) and (D) only
(4) (B) and (D) only
Answer: 3
Explanation:
- Strings with an even number of a's are Regular because a Finite acceptor(FA) can be drawn for them.
- Strings of a's with a length equal to a prime number — There are an infinite amount of prime numbers, and we can't create an FA for an infinite language.
-
This is not a Regular Set of all a's and b's palindromes.
We can't create FA for infinite language, thus this isn't Regular. -
Strings of a's with a precise square length.
We can't create FA for infinite language, thus this isn't Regular.
20. Consider the languages L1 = ϕ, and L2 = {1}. Which one of the following represents
L1* U L2* L1*?
(1) {ε}
(2) {ε,1}
(3) ϕ
(4) 1*
Answer: 4
Explanation:
L1 = ϕ, and L2 = {1}
L1 * is also ϕ
L2* will be 1*
so L1* U L2* L1* = 1*
21. Given the following statements :
(A) A class of languages that is closed under union and complementation has to be closed under intersection.
(B) A class of languages that is closed under union and intersection has to be closed under complementation.
Which of the following options is correct?
(1) Both (A) and (B) are false.
(2) Both (A) and (B) are true.
(3) (A) is true, (B) is false.
(4) (A) is false, (B) is true.
Answer: 3
Explanation:
A class of languages that is closed under union and complementation has to be closed under intersection. Correct.
A class of languages that is closed under union and intersection need not to be closed under complementation.
Statement II is Incorrect..
Hence, the answer is 3.
22. Let G = (V,T,S,P) be a context-free grammar such that every one of its productions is of the form A→v, with |v| = K>1. The derivation tree for any W ϵ L(G) has a height h such that
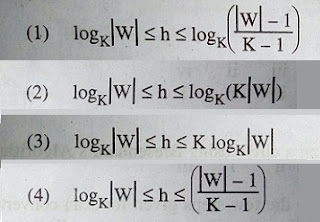
Answer: 4
Explanation:
It is a direct question , from peter linz
answer should be logkw <=h<= (|w|-1)/(k-1)
23. Given the following two languages:
L1 = {anbn|n≥0, n≠100}
L2 = {w ϵ {a,b,c}*| na(w) = nb(w) = nc(w)}
Which of the following options is correct?
(1) Both L1 and L2 are not context free language.
(2) Both L1 and L2 are context free language.
(3) L1 is context free language, L2 is not context free language.
(4) L1 is not context free language, L2 is context free language.
Answer: 3
Explanation:
L1 we can decompose as anbn |n<100 and anbn |n>100
First part regular ,second part DCFL , so it is obviously CFL
L2 needs two comparison n(a)= n(b) again n(b)=n(c) so we can not make a PDA for this
so it is CSL but not Context-Free
24. A recursive function h, is defined as follows:
|
h(m)=k, if m=0 = 1, if m=1 = 2h(m-1) + 4h(m-2), if m≥2 |
If the value of h(4) is 88 then the value of k is:
(1) 0
(2) 1
(3) 2
(4) -1
Answer: 3
Explanation:
|
h(4) = 88 88 = 2 h(3) + 4 h(2) = 2 [2 h(2) + 4 h(1)] + 4 h(2) = 8 h(2) + 8 h(1) = 8 (2 + 4 k) + 8 = 24 + 32 k i.e. k = 2 |
Hence 3 is correct.
25. Suppose there are n stations in a slotted LAN. Each station attempts to transmit with a probability P in each time slot. The probability that only one station transmits in a given slot is ..................
(1) nP(1-P)n-1
(2) nP
(3) P(1-P)n-1
(4) nP(1-P)n-1
Answer: 1
Explanation:
It can be derived using Binomial theorem of probability
NCi(p)i(1-p)n-1
Now 1 stations is sending with probability P ,and n-1 stations are not sending with probability 1-p
Now the probaility is= nC1 (p)1(1-p)n-1
=np(1-p)n-1






