Introduction
UGC NET Exam is one of the popular exams in India for people interested in research. Previous Year Questions are an excellent option to learn about the exam pattern. By solving the PYQs, you will get a basic idea about your preparation. You can evaluate your weak areas and work on them to perform better in the examination. In this article, we have given the questions of UGC NET 2016 July Paper-II. We have also explained every problem adequately to help you learn better.
Note: This article contains Q.No. 1 to Q.No. 25 out of the 75 questions asked in NET july 2016 paper II. The solution to Q.No. 26 to Q.No. 50 can be found in the July 2016 Paper-II Part-2 article and the solution of Q.No. 51 to Q.No. 75 can be found in the July 2016 Paper-II Part-3 article.
Questions 1 to 25
(1) Which of the following is a sequential circuit?
(A) Multiplexer (B) Decoder
(C) Counter (D) Full adder
Answer: C
Multiplexer, Decoder and Full adder are examples of combinational circuits while counter is a Sequential circuit.
(2) 8085 microprocessor has ............. hardware interrupts.
(A) 2 (B) 3
(C) 4 (D) 5
Answer: D
The 8085 microprocessor has 5 hardware interrupts which are named as TRAP, RST 7.5, RST 6.5, RST 5.5 and INTR. 8086 microprocessor has 2 hardware interrupts named as NMI and INTR.
(3) Which of the following in 8085 microprocessor performs
HL = HL + DE ?
(A) DAD D (B) DAD H
(C) DAD B (D) DAD SP
Answer: A
DAD will perform Double addition (16 bit) between HL pair and any other pair of registers. Among HL, BC, DE and SP; B, H and D registers will be used first.
So, DAD H will do HL = HL + HL;
DAD B will do HL = HL + BC;
DAD D will do HL = HL + DE;
SP is stack pointer and it is not a pair register, DAD SP will do HL = HL + SP;
(4) The Register that stores all interrupt requests is:
(A) Interrupt mask register
(B) Interrupt service register
(C) Interrupt request register
(D) Status register
Answer: C
The register that stores all interrupt requests is Interrupt request register.
Interrupt mask register is a read and write register which enables or masks interrupts from being triggered on the external pins of the Cache Controller.
Interrupt service registers handle the interrupt and service them according to priority and other conditions.
Status register is a hardware register that contains information about the state of the processor
(5) The ............... addressing mode is similar to register indirect addressing mode, except that an offset is added to the contents of the register. The offset and register are specified in the instruction.
(A) Base indexed
(B) Base indexed plus displacement
(C) Indexed
(D) Displacement
Answer: D
The displacement addressing mode is similar to register indirect addressing mode, except that an offset is added to the contents of the register. The offset and register are specified in the instruction.
(6) In ............. method, the word is written to the block in both the cache and main memory, in parallel.
(A) Write through (B) Write back
(C) Write protected (D) Direct mapping
Answer: A
In the write through method, the word is written to the block in both the cache and main memory, in parallel and in the write back method the word is written to the block in cache but actual update into the corresponding location in main memory only at specified intervals or under certain conditions.
(7) Which of the following statements concerning Object-Oriented databases is FALSE?
(A) Objects in an object-oriented database contain not only data but also methods for processing the data.
(B) Object-oriented databases store computational instructions in the same place as the data.
(C) Object-oriented databases are more adapt at handling structures (analytical) data than relational databases.
(D) Object-oriented databases store more types of data than relational databases and access that data faster.
Answer: C
Object-oriented databases are more adept at handling structured (analytical) data than relational databases. This statement is incorrect.
(8) In distributed databases, location transparency allows for database users, programmers and administrators to treat the data as if it is at one location. A SQL query with location transparency needs to specify:
(A) Inheritances (B) Fragments
(C) Locations (D) Local formats
Answer: B
In SQL query with location transparency, the end user must specify the database fragment name but does not need to specify where those fragments are located.
(9) Consider the relations R(A,B) and S(B,C) and the following four relational algebra queries over R and S:
I. πA,B(R⋈S)
II. R⋈πB(S)
III. R∩(πA(R) Χ πB(S))
IV. πA,R.B(R Χ S) where R.B refers to the column B in table R.
One can determine that:
(A) I, III and IV are the same query.
(B) II, III and IV are the same query.
(C) I, II and IV are the same query.
(D) I, III and III are the same query.
Answer: D
In query no. 4, there is no equal to condition check while in rest R.B = S.B is checked. Hence the correct answer will be option D.
(10) Which of the following statements is TRUE?
D1: The decomposition of the schema R(A,B,C) into R1(A,B) and R2(A,C) is always lossless.
D2: The decomposition of the schema R(A,B,C,D,E) having AD→B, C→DE, B→AE, AE→C into R1(A,B,D) and R2(A,C,D,E) is lossless.
(A) Both D1 and D2 (B) Neither D1 and D2
(C) Only D1 (D) Only D2
Answer: D
Only D2 is True because AD is key and present in both the tables.
D1 is not always true because FD's are not given and if we take B->A and C->A then it is lossy decomposition because no common attributes contain a key from one of the tables.
(11) Consider the following ORACLE relations:
R(A,B,C) = {<1,2,3>, <1,2,0>, <1,3,1>, <6,2,3>, <1,4,2>, <3,1,4>}
S(B,C,D) = {<2,3,7>, <1,4,5>, <1,2,3>, <2,3,4>, <3,1,4>}
Consider the following two SQL queries SQ1 and SQ2:
SQ1: SELECT R.B, AVG(S.B)
FROM R, S
WHERE R.A = S.C AND S.D < 7
GROUP BY R.B;
SQ2: SELECT DISTINCT S.B, MIN (S.C)
FROM S
GROUP BY S.B
HAVING COUNT (DISTINCT S.D) > 1;
If M is the number of tuples returned by SQ1 and N is the number of tuples returned by SQ2 then
(A) M=4, N=2 (B) M=5, N=3
(C) M=2, N=2 (D) M=3, N=3
Answer: A
Output after RxS in SQ1
| R.A | R.B | R.C | S.B | S.C | S.D |
| 1 | 2 | 3 | 3 | 1 | 4 |
| 1 | 2 | 0 | 3 | 1 | 4 |
| 1 | 3 | 1 | 3 | 1 | 4 |
| 1 | 4 | 2 | 3 | 1 | 4 |
| 3 | 1 | 4 | 2 | 3 | 7 |
| 3 | 1 | 4 | 2 | 3 | 4 |
Final output of SQ1 :
| R.B | AVG(S.B) |
| 2 | 3 |
| 3 | 3 |
| 4 | 3 |
| 1 | 2 |
SQ2 output :
| S.B | MIN(S.C) |
| 1 | 2 |
| 2 | 3 |
(12) Semi-join strategies are techniques for query processing in distributed database system. Which of the following is a semi-join technique?
(A) Only the joining attributes are sent from one site to another and then all of the rows are returned.
(B) All of the attributes are sent from one site to another and then only the required rows are returned.
(C) Only the joining attributes are sent from one site to another and then only the required rows are returned.
(D) All of the attributes are sent from one site to another and then only the required rows are returned.
Answer: C
Semi-join strategies are techniques for query processing in distributed database system. In which only the joining attributes are sent from one site to another and then only the required rows are returned.
(13) Consider the Breshenham’s circle generation algorithm for plotting a circle with centre (0,0) and radius ‘r’ units in first quadrant. If the current point is (x1,y1) and decision parameter is pi then what will be the next point (xi+1,yi+1) and updated decision parameter pi+1 for pi ≥ 0
(A) xi+1 = xi + 1 yi+1 = yi pi+1 = pi + 4xi + 6
(B) xi+1 = xi + 1 yi+1 = yi - 1 pi+1 = pi + 4(xi - yi) + 10
(C) xi+1 = xi yi+1 = yi - 1 pi+1 = pi + 4(xi - yi) + 6
(D) xi+1 = xi - 1 yi+1 = yi pi+1 = pi + 4xi + 10
Answer: B
Bresenham’s Algorithm
We cannot display a continuous arc on the raster display. Instead, we have to choose the nearest pixel position to complete the arc.
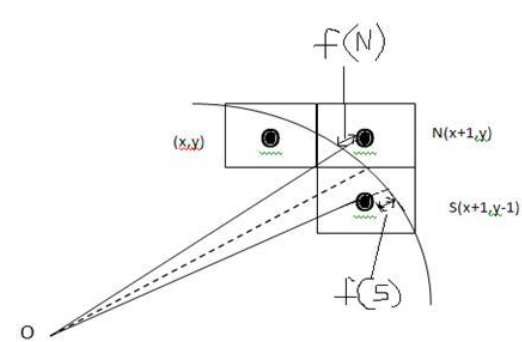
From the following illustration, you can see that we have put the pixel at (X, Y) location and now need to decide where to put the next pixel − at N (X+1, Y) or at S (X+1, Y-1).
Source: tutorialspoint
This can be decided by the decision parameter d.
1. If d <= 0, then N(X+1, Y) is to be chosen as next pixel.
2. If d > 0, then S(X+1, Y-1) is to be chosen as the next pixel.
Algorithm:
Step 1 − Get the coordinates of the center of the circle and radius, and store them in x, y, and R respectively. Set P=0 and Q=R.
Step 2 − Set decision parameter D = 3 – 2R.
Step 3 − Repeat through step-8 while X < Y.
Step 4 − Call Draw Circle (X, Y, P, Q).
Step 5 − Increment the value of P.
Step 6 − If D < 0 then D = D + 4x + 6.
Step 7 − Else Set Y = Y - 1, D = D + 4(X-Y) + 10.
Step 8 − Call Draw Circle (X, Y, P, Q).
(14) A point P(5,1) is rotated by 90 degree about a pivot point (2,2). What is the coordinate of new transformed point P’ ?
(A) (3,5) (B) (5,3)
(C) (2,4) (D) (1,5)
Answer: A
When the point is rotated through 90∘ clockwise about the origin, the point M(h,k) takes the image M ′ (k,−h). Therefore, the new position of point M(−2,3) will become M ′ (3,2).
(15) Let R be the rectangular window against which the lines are to be clipped using 2D Sutherland-Cohen line clipping algorithm. The rectangular window has lower left-hand corner at (-5,1) and upper right-hand corner at (3,7). Consider the following three lines for clipping with the given end point co-ordinates:
Line AB: A(-6,2) and B(-1,8)
Line CD: C(-1,5) and D(4,8)
Line EF: E(-2,3) and F(1,2)
Which of the following line(s) is/are candidate for clipping?
(A) AB (B) CD
(C) EF (D) AB and CD
Answer: D
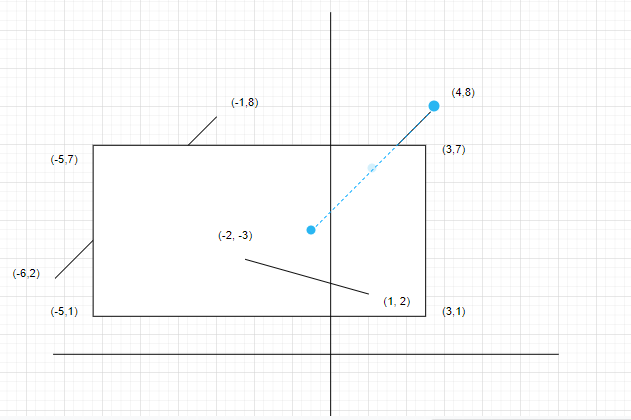
As we can see only AB and CD are candidates for line clipping.
(16) In perspective projection, if a line segment joining a point which lies in front of the viewer to a point in back of the viewer is projected to a broken line of infinite extent. This is known as ...................
(A) View confusion (B) Vanishing point
(C) Topological distortion (D) Perspective foreshortening
Answer: C
In perspective projection, if a line segment joining a point which lies in front of the viewer to a point in back of the viewer is projected to a broken line of infinite extent. This is known as topological distortion.
(17) Let us consider that the original point is (x,y) and new transformed point is (x’,y’). Further, Shx and Shy are shearing factors in x and y directions. If we perform the y-direction shear relative to x=xref then the transformed point is given by ............
(A) x’ = x + Shx . (y - yref) y’ = y
(B) x’ = x y’ = y . Shx
(C) x’ = x y’ = Shy(x - xref) + y
(D) x’ = Shy . y y’ = y . (x - xref)
Answer: C
if we perform x direction shear with reference to y axis, then
x′= x + Shx.(y−yref); y′=y
if we perform y direction shear with reference to x axis, then
x′ = x; y′ = Shy(x−xref) + y
(18) Which of the following statement(s) is/are correct with reference to curve generation?
I. Hermite curves are generated using the concepts of interpolation.
II. Bezier curves are generated using the concepts of approximation.
III. The Bezier curves lies entirely within the convex hull of its control points.
IV. The degree of Bezier curve does not depend on the number of control points.
(A) I, II and IV only (B) II and III only
(C) I and II only (D) I, II and III only
Answer: D
The degree of Bezier curve does not depend on the number of control points. Only this statement is incorrect. All the other three statements are true.
(19) Given the following statements:
(a) To implement Abstract Data Type, a programming language require a syntactic unit to encapsulate type definition.
(b) To implement ADT, a programming language requires some primitive operations that are built in the language processor.
(c) C++, Ada, Java 5.0, C#2005 provide support for parameterised ADT.
Which one of the following options is correct?
(A) (a), (b) and (c) are false.
(B) (a) and (b) are true; (c) are false.
(C) (a) is true; (b) and (c) are false.
(D) (a), (b) and (c) are true.
Answer: D
To implement Abstract Data Type, a programming language require a syntactic unit to encapsulate type definition.
To implement ADT, a programming language requires some primitive operations that are built in the language processor.
C++, Ada, Java 5.0, C#2005 provide support for parameterised ADT.
All these statements are correct.
(20) Match the following types of variables with the corresponding programming languages:
(a) Static variables (i) Local variables in Pascal
(b) Stack dynamic (ii) All variables in APL
(c) Explicit heap dynamic (iii) Fortran 77
(d) Implicit heap dynamic (iv) All objects in JAVA
Codes:
(a) (b) (c) (d)
(A) (i) (iii) (iv) (ii)
(B) (iv) (i) (iii) (ii)
(C) (iii) (i) (iv) (ii)
(D) (ii) (i) (iii) (iv)
Answer: C
Static variables are used in Fortran 77
Stack dynamic are local variables in Pascal
Explicit heap dynamic are all objects in JAVA
Implicit heap dynamic are all variables in APL
(21) Which of the following is false regarding the evaluation of computer programming languages?
(A) Application oriented features (B) Efficiency and Readability
(C) Software development (D) Hardware maintenance cost
Answer: D
Efficiency and Readability, Application oriented features and Software development are regarding to the evaluation of computer programming languages. But Hardware maintenance costis not regrading to the evaluation of computer programming languages.
(22) The symmetric difference of two sets S1 and S2 is defined as
S1ΘS2 = {x|xϵS1 or xϵS2, but x is not in both S1 and S2}
The nor of two languages is defined as
nor (L1,L2) = {w|w ∉ L1 and w|w ∉ L2}
Which of the following is correct?
(A) The family of regular languages is closed under symmetric difference but not closed under nor.
(B) The family of regular languages is closed under nor but not closed under symmetric difference.
(C) The family of regular languages are closed under both symmetric difference and nor.
(D) The family of regular languages are not closed under both symmetric difference and nor.
Answer: C
S1⊕S2= S1cS1cS2 + S1S2cS2c
Regular languages are closed under intersection, complementation and
union and hence they are closed under set difference as well.
nor(L1+L2)= L1c.L2c (from demorgan's law)
Here . represents intersection.
Regular languages are closed under complementation and intersection and hence they are closed under nor as well.
(23) The regular expression for the complement of the language L = {anbm|n≥4, m≤3} is:
(A) (λ + a + aa + aaa)b* + a*bbbb* + (a + b)*ba(a + b)*
(B) (λ + a + aa + aaa)b* + a*bbbbb* + (a + b)*ab(a + b)*
(C) (λ + a + aa + aaa) + a*bbbbb* + (a + b)*ab(a + b)*
(D) (λ + a + aa + aaa)b* + a*bbbbb* + (a + b)*ba(a + b)*
Answer: D
The complement of the language L = {anbm|n ≥ 4, m ≤ 3} is L` = {anbm|n < 4} U {anbm|m > 3}:
L` = Universal set – L.
L` = Universal set – {anbm|n ≥ 4, m ≤ 3}
= (λ + a + aa + aaa)b* + a*bbbbb* + (a + b)* ba(a + b)*
Option (D) is giving freedom on constraints on number of a’s and number of b’s.
(24) Consider the following two languages:
L1 = {0i1j | gcd(i,j)=1}
L2 is any subset of 0*.
Which of the following is correct?
(A) L1 is regular and L2* is not regular
(B) L1 is not regular and L2* is regular
(C) Both L1 and L2* are regular languages
(D) Both L1 and L2* are not regular languages
Answer: B
L1 = {0i1j| gcd (i, j) = 1}:
There are infinite pair having gcd 1. We can’t design FA for such language. That’s why L1 is not regular.
L2 is any subset of 0*, we can construct FA for any subset of single alphabet. That’s why L2 is regular.
(25) If link transmits 4000 frames per second and each slot has 8 bits, the transmission rate of circuit of this TDM is ...............
(A) 64 Kbps (B) 32 Mbps
(C) 32 Kbps (D) 64 Mbps
Answer: C
Transmission rate = frame rate * no of bits in a slot.
Frame rate = 4000 frames per second
# of bits in a slot = 8 bit
TDM = 4000 * 8 bps = 32 Kbps.
FAQs
What is the UGC NET exam?
UGC NET is a national-level exam organized by UGC to determine the eligibility of the candidates for lectureship and JRF.
What is the maximum number of attempts for the UGC NET examination?
There is no bar on the number of attempts of this examination. Candidates can appear for the examination as long as they are eligible.
How can solving PYQs help in my exam preparation?
Solving PYQs will give you a good idea about the exam pattern and help you identify your weak topics to prepare them better for the examination.
How many papers are there in the UGC NET exam?
There are two papers, and the candidates get 3 hours for both papers. There are 150 questions in UGC NET combining both papers.