Introduction
It is more than likely that a rookie programmer might execute some sensitive code at times and that might lead to system failure and erroneous functioning of the operating system. Thus to ensure the proper functioning of the operating system, we must be able to distinguish between the execution of the user system code and the operating system code. For this purpose, we have Dual mode in the operating system. Before moving on to the privileged and non-privileged instructions, let’s get a quick overview of dual-mode in OS.
Also See, FCFS Scheduling Algorithm, Multiprogramming vs Multitasking
Dual Mode in OS
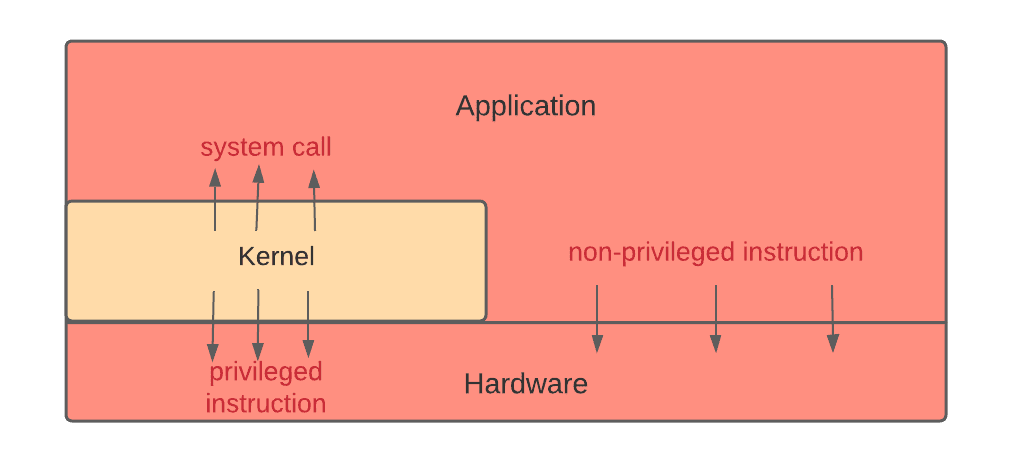
The dual mode in the operating system consists of basically two modes of operation- User mode (also called non-privileged mode) and Kernel mode (also called supervisor mode, system mode, and privileged mode). When a user is running an application, the system is in user mode. However, when a user application requests to access a file (for reading and writing data), the system needs to switch from the user mode to the kernel mode through a system call since the files reside in the secondary memory, and the user can’t access them directly. After executing the system call, the system returns to the user mode.
Also read - fork() system call
Note: A system call allows a user to communicate with the kernel and requests operations that can be carried out by the kernel only.
We have the mode bit to find out whether a task is getting executed on behalf of the user or the operating system. A mode bit is a bit that is added to the computer hardware to indicate the current mode: 0 represents the system is in kernel mode, and 1 represents the system is in user mode.

The life cycle of instruction
Since we have discussed the dual mode in the operating system, we are in a state to understand the life cycle of instruction in the operating system.
Initially, the instructions are executed in the kernel mode, with the control residing in the operating system. As soon as a user starts an application, the control is switched to the user mode. Whenever there is a system call, interrupt, or trap, the control is eventually transferred to kernel mode. The control is returned to the instruction following the system call when the system call is executed. In this way, all instructions are executed.
Now we will discuss what exactly privileged and non-privileged instructions are: