Introduction
UGC NET Exam is a very popular exam in India for people interested in the research domain. NET(National Eligibility Test) is conducted by NTA (NATIONAL TESTING AGENCY) to identify qualified candidates for Assistant Professor positions in colleges and universities, as well as Junior Research Fellowships (JRF). This article will discuss the UGC NET Exam of June 2013 paper III solutions from questions 1 to 25. You can also checkout the remaining questions and solutions solution of this paper in UGC NET June 2013 Paper III Part 2 and UGC NET June 2013 Paper III Part 3.
-
The Software Maturity Index (SMI) is defined as SMI = [Mf – (Fa + Fc + Fd) ] /Mf Where Mf = the number of modules in the current release. Fa = the number of modules in the current release that have been added. Fc = the number of modules in the current release that have been changed. Fd = the number of modules in the current release that have been deleted. The product begins to stabilize when
- SMI approaches 1
- SMI approaches 0
- SMI approaches – 1
-
None of the above
Ans- A
Explanation- A software maturity index (SMI) was proposed by IEEE to indicate the stability of a software product (based on changes that occur for each release of the product). The formula mentioned in the question is used to compute SMI. The question also includes an explanation of the formula. When the SMI reaches 1.0, the product begins to stabilize. The Software Maintenance Index (SMI) can also be used to plan software maintenance tasks.
-
Match the following:
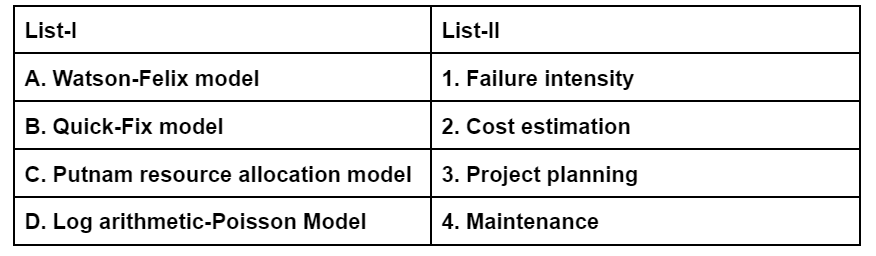
A B C D- 2 1 4 3
- 1 2 4 3
- 2 1 3 4
-
2 4 3 1
ANS-D
Explanation:
It provides a relationship between delivered source lines of code L and effort E and is given by the equation:-
F = 5.25 - L 0.9
Similarly, the duration of development D in months is given by:
D = 4.1 - L 0.36.
Quick Fix Model - It is ad hoc for maintaining software. It is a firefighting approach, waiting for the problem to occur and then trying to fix it.
Putnam Model describes the time and effect required to finish a software project of a specified size.
Logarithmic Poisson Model - It is a software reliability model that predicts expected failures (and hence related reliability quantities).
-
________ is a process model that removes defects before they can precipitate serious hazards.
- Incremental model
- Spiral model
- Cleanroom software engineering
-
Agile model
Ans- C
Explanation: CSE (cleanroom software engineering) is a process paradigm for removing problems before they become dangerous. Because this is the exact definition of CSE, the right answer is C.
-
Equivalence partitioning is a ________ method that divides the input domain of a program into classes of data from which test cases can be derived
- White-box testing
- Black-box testing
- Orthogonal array testing
-
Stress testing
Ans- B
Explanation:The question asks what equivalence partitioning is. However, we must determine whether it falls within the category of white-box, black-box, or the other two testing methods. Equivalence partitioning is a type of black-box test. Boundary-value analysis, classification trees, cause-effect graphs, and other black-box testing approaches are examples.
-
The following three golden rules:
Place the user in control
Reduce the user՚s memory load
Make the interface- User satisfaction
- Good interface design
- Saving system՚s resources
-
None of these
Ans- B
Explanation: These rules are known as Mandel’s Golden Rules
-
Software safety is a ________ activity that focuses on the identification and assessment of potential hazards that may affect software negatively and cause an entire system to fail.
- Risk mitigation, monitoring and management
- Software quality assurance
- Software cost estimation
-
Defect removal efficiency
Ans- B
Explanation: Software safety and hazard analysis are software quality assurance activities that focus on identifying and assessing potential hazards that could have a negative influence on software and cause a system to fail.
-
The “PROJECT” operator of a relational algebra creates a new table that has always
- More columns than columns in original table
- More rows than the original table
- Same number of rows as the original table
-
Same number of columns as the original table
Ans- C
Explanation:So, based on the available options, the PROJECT operator cannot build a table with more columns than the original table. The same number of columns were ruled out as well. It is also incorrect to have more rows than the original table. As a result, the table will have the same amount of rows as the original table, but fewer columns. As a result, C is the correct answer.
-
The employee information of an Organization is stored in the relation: Employee (name, sex, salary, deptname) Consider the following SQL query Select deptname from Employee Where sex = ‘M’ group by deptname having avg (salary) > {select avg (salary) from Employee} Output of the given query corresponds to
- Average salary of employee more than average salary of the organization.
- Average salary less than average salary of the organization.
- Average salary of employee equal to average salary of the organization.
-
Average salary of male employees in a department is more than average salary of the organization
Ans- D
Explanation: The query has a greater than sign, which we all know what it means. Options B and C state that the average pay is less and equal, respectively. As a result, B and C are both ruled out. Option A states that the Employee's average wage is higher than the organization's average salary. However, there is a where clause in the query that says sex='M,' implying that the average salary of male employees is higher than the organization's average salary. As a result, option D is the proper response.
-
For a database relation R (a, b, c, d) where the domains of a, b, c, d include only the atomic values. The functional dependency a ⇾ c, b ⇾ d holds in the following relation
- In 1NF not in 2NF
- In 2NF not in 3NF
- In 3NF
-
In 1NF
Ans- A
Explanation: If the domain of each attribute only contains atomic values, the relation is in the first normal form. It implies that atomicity must exist in the relationship. As a result, the question expressly states the same. Because the domains of a,b,c,d only include atomic values, 1NF holds true, but the question is whether 2NF holds true. If a relation is in the first normal form, it will be in the second normal form, and all non-primary key attributes must be functionally reliant on the primary key property
-
Match the following:
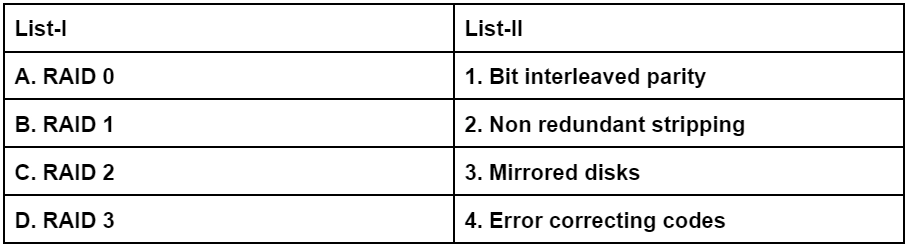
A B C D- 4 1 2 3
- 3 4 1 2
- 3 1 4 2
-
3 2 4 1
Ans- None of these
Explanation: The following are one-liners that describe various RAIDs and their specifications. There is no redundancy in RAID 0. It's the JBOD (Just a Bunch of Disks) Mirroring or shadowing in RAID 1 RAID 2 - Error-correcting codes similar to those found in memory are applied to drives. Bit interleaved parity (RAID 3)
-
The golden ratio ϕ and its conjugate – ϕ both satisfy the equation
- x3 – x – 1 = 0
- x3 + x – 1 = 0
- x2 – x – 1 = 0
-
x2 + x – 1 = 0
Ans- C
ExplanationT: he ratio of a/b is called golden ration if (a+b)/b =a/b where [a/b=x ]1+(b/a) = (a/b)=01=(a/x)=x ⇒ x^2-x-x=0
-
The solution of recurrence relation, T(n) = 2T(floor ( n)) + logn is
- O(n log log logn)
- O(n log logn)
- O(log logn)
-
O(logn log long)
Ans- D
Explanation:
T(n)=2T(⎷n)+logn
Let n=2kT(2k)=2T(2k/2)+kLet T(2k)=S(k)So S(k)=2S(k/2)+kUsing Master TheoremS(k)=O(k log k)So T(n)=O(logn log logn)
-
In any n-element heap, the number of nodes of height h is
- less than equal to [ n/2^h ]
- greater than [ n/2^h ]
- greater than[ n/(2^h +1)]
-
less than equal to [ n/(2^h +1)]
Ans- D
Explanation: Therom
-
A data file of 1,00,000 characters contains only the characters g-l, with the frequencies as indicated in table : g h i j k l Frequency in thousand 45 13 12 16 9 5 using the variable-length code by Huffman codes, the file can be encoded with
- 2,52,000 bits
- 2,64,000 bits
- 2,46,000 bits
-
2,24,000 bits
Ans- D
Explanation
Probability of g.= 45/100=.45
Probability of j= 16/100=.16.
Probability of H= .13
Probability of i=.12
Probability of k=.9
Probability of l=.5.
A tree is formed.
G takes I bit so it takes 45000 bits.
J takes 2 bits so it takes 32000 bits.
H takes 3 bits so it takes 39000 bits.
I takes 4 bits so it takes 48000bits.
K takes 5 bits so it takes 45000bits.
L takes 5 bits so it takes 25000bits
So it takes 224000 bits.
-
A vertex cover of an undirected graph G(V, E) is a subset V1 ⊆ V vertices such that
- Each pair of vertices in V1 is connected by an edge
- If (u, v) ∈ E then u ∈ V1 and v ∈ V1
- If (u, v) ∈ E then u ∈ V1 or v ∈ V1
-
All pairs of vertices in V1 are not connected by an edge
Ans- C
Explanation:
A set of vertices such that each edge of the graph is incident to at least one vertex of the set.
Set consists of rest of nodes is called independent set.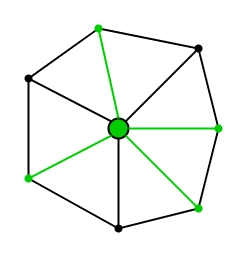
Every planar graph has a vertex cover of size at most 3n/4
-
In a fully connected mesh network with n devices, there are ________ physical channels to link all devices.
- n(n–1)/2
- n(n+1)/2
- 2n
-
2n+1
Ans- A
Explanation- Suppose there are N devices in the network. In a mesh network, every device can connect to the remaining (n-1) device.
- Here Link Between two devices will be counted 2 times.
- Hence,Total Number of Physical channel required to Link between all device= n(n−1)2
-
Hence,Option(A)n(n−1)2.
-
The baud rate of a signal is 600 baud/second. If each signal unit carries 6 bits, then the bit rate of a signal is ________.
- 3600
- 100
- 6/600
-
None of the above
Ans- A
Explanation- Bit rate = baud rate X n
- Baud rate = 600 baud/second.
- n= number of bits = 6
- bit rate = 600 X 6 = 3600
-
So, the correct answer is A
-
Match the following : a. Data link layer i. Flow control b. Network layer ii. Node to node delivery c. Transport layer iii. Mail services d. Application layer iv. Routing Codes : a b c d
- ii i iv iii
- ii iv i iii
- ii i iii iv
-
ii iv iii I
Ans- B
Explanation- Data Link layer is the protocol layer that transfers data between adjacent network nodes in a wide area network.
- Network Layer is responsible for packet forwarding including routing through intermediate routers.
- Transport Layer provides convenient services such as connection-oriented data stream support, reliability, flow control, and multiplexing
-
Application layer is an abstraction layer reserved for communications protocols and methods designed for the process to process communications across an Internet Protocol(IP) computer network(Mail Services)
-
An image is 1024∗800 pixels with 3 bytes/pixel. Assume the image is uncompressed. How long does it take to transmit it over a 10-Mbps Ethernet ?
- 196.6 seconds
- 19.66 seconds
- 1.966 seconds
-
0.1966 seconds
Ans- C
Explanation- Size of an Image = 1024 x 800 x 3 bytes
- = 2457600 bytes
- = 19660800 bits
- The time it takes to translate the image over 10Mbps ethernet will be:
- 10,000,000 bits = 1 second
- 19660800 bits = 19660800/10000000
-
= 1.966 seconds
-
The __ ______ measures the relative strengths of two signals or a signal at two different points.
- frequency
- attenuation
- throughput
-
Decibel
Ans-D
Explanation: The loss or gain in signal strength is measured in units of decibel. The decibels(dB) measure the relative strength of two signals or one signal at two different points The decibel is negative if a signal is attenuated and positive if the signal is amplified.
-
Which one of the following media is multidrop ?
- Shielded Twisted pair cable
- Unshielded Twisted pair cable
- Thick Coaxial cable
-
Fiber Optic cable
Ans- C
Explanation: A multipoint (also called multidrop) connection is one in which more than two specific devices share a single link. In a multipoint environment, the capacity of the channel is shared, either spatially or temporally. If several devices can use the link simultaneously, it is a spatially shared connection. If users must take turns, it is a timeshare connection. Thick Coaxial cable is one of the above media is multi-drop
-
What is the baud rate of the standard 10 Mbps Ethernet ?
- 10 megabaud
- 20 megabaud
- 30 megabaud
-
40 megabaud
Ans- B
Explanation- The ethernet uses Manchester encoding which means it has two signal periods per sending bit.
- The data rate of the standard ethernet is 10Mbps.
-
So the baud rate is twice that i.e. 20 Megabaud
-
At any iteration of simplex method, if Δj (Zj – Cj) corresponding to any non-basic variable Xj is obtained as zero, the solution under the test is
- Degenerate solution
- Unbounded solution
- Alternative solution
-
Optimal solution
Ans- C
Explanation: When the objective function is parallel to a non-redundant binding constraint (i.e., a constraint that is satisfied as an equation at the optimal solution), the objective function can assume the same optimal value at more than one solution point, thus giving rise to alternative optima. An LPP is degenerate if, in a basic feasible solution, one of the basic variables takes a zero value.
-
A basic feasible solution to a m-origin, n-destination transportation problem is said to be _________ if the number of positive allocations are less than m + n – 1.
- degenerate
- non-degenerate
- unbounded
-
unbalanced
Ans- A
Explanation: Feasible soln should have a number of positive allocations equal to m+n-1. If it is less than this then soln is degenerate(degeneracy problem ) and soln is not feasible
-
The total transportation cost in an initial basic feasible solution to the following transportation problem using Vogel’s Approximation method is
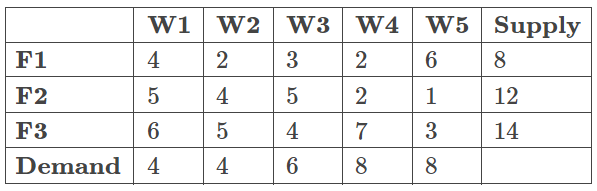
- 76
- 80
- 90
- 96
Ans- B
Explanation: Vogel's Approximation Method is an iterative approach for determining a basic workable transportation solution. The following is the algorithm for Vogel's Approximation Method (VAM):
Step 1: Identify the boxes in each row with the lowest and next-lowest transportation costs, then put the difference (Penalty) along the table's side against the appropriate row.
Step 2: In each column, identify the boxes with the lowest and next-lowest transportation costs, and put the difference (Penalty) along the table's side against the relevant column. If the minimum price appears two or more times in a row or column, select the exact cost as the minimum, and the penalty will be zero.
Step 3: 1. Break ties arbitrarily by identifying the row and column with the highest penalty. As feasible the specified row or column should be allocated to the variable with the lowest cost. Make the necessary adjustments to supply and demand, and then cross out the satisfied row or column. If a row and column are both satisfied at the same time, only one is crossed out, and the remaining row or column is given a supply or demand of zero.
2. If the highest magnitude of two or more penalty costs is the same, choose any one of them.
Step 4: 1. Stop if there is precisely one row or column with zero supply or demand left uncrossed out.
2. If just one row or column with positive supply or demand remains uncrossed out, use the Least-Cost Method to identify the basic variables in that row or column.
3. The Least-Cost Method is used to identify the zero basic variables if all uncrossed out rows or columns have (remaining) zero supply or demand. Stop.
If not, proceed to Step 1.
Using the process outlined above, we arrive at an answer of 80.
FAQs
What is UGC NET exam for?
The National Eligibility Test (NET) is a test administered by the University Grants Commission (UGC) to determine whether Indian nationals are eligible for Assistant Professorships, Junior Research Fellowships, or both in Indian universities and colleges.
What is UGC NET exam eligibility?
If you hold a Master's Degree or equivalent in Humanities (including languages), Social Science, Computer Science and Applications, Electronic Science, etc., you are eligible to take the UGC NET test.
Is PhD compulsory for net?
To teach in central institutions, one must hold a PhD or have completed the UGC NET qualification exam, according to UGC regulations. The UGC, on the other hand, intends to scrap the regulation requiring experts to be hired and replace it with specific titles such as professor of practise and associate professor of practise.
How many papers are there in the UGC NET exam?
There are two papers, and the candidates get 3 hours for both papers. There are 150 questions in UGC NET combining both papers.
What is the full form of UGC NET?
UGC stands for University Grants Commission, and NET stands for National Eligibility Test.