Arcesium interview experience Real time questions & tips from candidates to crack your interview
SDE - Intern
Arcesium
4 rounds | 5 Coding
problems
Interview preparation journey
Preparation
Duration: 6 months
Topics: Data Structures, Algorithms, Operating Systems, DBMS, OOPS, Digital Logic and Design
Tip
Tip 1 : Focus on the core computer science knowledge, because Fintech firms grind you on that
Tip 2 : Practice at least 300 questions covering all topics
Tip 3 : Do at least one good project which you can explain thoroughly
Application process
Where: Campus
Eligibility: Above 7 CGPA
Resume tip
Tip 1 : Mention your academic achievements on your resume
Tip 2 : Mention only those projects which you are able to explain.
Interview rounds
01
Round
Hard
Online Coding Interview
Duration90 minutes
Interview date16 Oct 2019
Coding problem2
The OA had 20 aptitude questions and 2 coding questions.
1. Largest Component Size by Common Factor
Hard
50m average time
50% success
0/120
Asked in companies

You are given an array of positive integers, ‘VERTICES’ that represent the vertices in a graph. Two vertices, ‘V1’ and ‘V2’, have an edge between them if and only if ‘V1’ and ‘V2’ share a common factor greater than 1. Your task is to return the size of the largest connected component in the graph.
Problem approach
The idea is to use a disjoint set data structure. We will maintain a disjoint set where different numbers are linked together if and only if they have a common factor greater than 1. So, we have to link each element in ‘VERTICES’ with all its factors greater than 1.
2. Reverse Nodes in k-Group
Hard
56m average time
30% success
0/120
Asked in companies



You are given a Singly Linked List of integers and an integer array 'B' of size 'N'. Each element in the array 'B' represents a block size. Modify the linked list by reversing the nodes in each block whose sizes are given by the array 'B'.
Note:
1. If you encounter a situation when 'B[i]' is greater than the number of remaining nodes in the list, then simply reverse the remaining nodes as a block and ignore all the block sizes from 'B[i]'.
2. All block sizes are contiguous i.e. suppose that block 'B[i]' ends at a node cur, then the block 'B[i+1]' starts from the node just after the node cur.
Example
Linked list: 1->2->3->4->5
Array B: 3 3 5
Output: 3->2->1->5->4
We reverse the first block of size 3 and then move to block 2. Now, since the number of nodes remaining in the list (2) is less than the block size (3), we reverse the remaining nodes (4 and 5) as a block and ignore all the block sizes that follow.
Problem approach
This is a standard linked list + recursion problem. Keep on reversing the linked list in the group of k elements. and the last element of ith group will point to the first element of i+1th group. Store the head pointer and at the end, return the head.
02
Round
Easy
Face to Face
Duration60 minutes
Interview date18 Oct 2019
Coding problem1
The interviewer was an SDE-2 in Arcesium and this round mainly started with introduction and then he asked one programming question. You have to write code on paper, so please prepare for that also.
1. Bridges In A Graph
Moderate
25m average time
65% success
0/80
Asked in companies


Given an undirected graph of V vertices and E edges. Your task is to find all the bridges in the given undirected graph. A bridge in any graph is defined as an edge which, when removed, makes the graph disconnected (or more precisely, increases the number of connected components in the graph).
For Example :
If the given graph is :
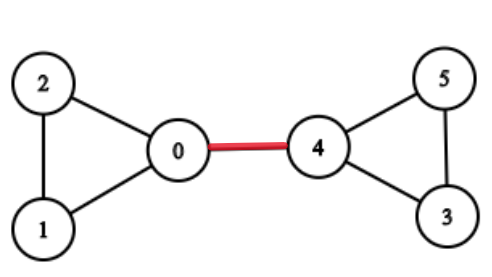
Then the edge between 0 and 4 is the bridge because if the edge between 0 and 4 is removed, then there will be no path left to reach from 0 to 4.and makes the graph disconnected, and increases the number of connected components.
Note :
There are no self-loops(an edge connecting the vertex to itself) in the given graph.
There are no parallel edges i.e no two vertices are directly connected by more than 1 edge.
Problem approach
The brute force approach to find all the bridges in a given graph is to check for every edge if it is a bridge or not, by first not considering current edge is not in given graph and then checking if the vertices that it was connecting are still connected or not, using DFS(DepthFirst Search).
03
Round
Medium
Face to Face
Duration60 minutes
Interview date21 Oct 2019
Coding problem1
There were two interviewers in this round. They started with some basic introduction and asked some questions related to my college projects and then jumped on to the coding question.
1. Bipartite Graph
Moderate
0/80
Asked in companies


Given an undirected graph of ‘V’ vertices (labeled 0,1,..., V-1) and ‘E’ edges . Your task is to check whether the graph is bipartite or not.
A bipartite graph is a graph whose vertices can be divided into two sets such that each edge of the graph connects one vertex from the first set and another vertex from the second set.
We can also define a bipartite graph as a graph which can be colored using two colors such that no two adjacent vertices have the same color.
For example:
Input:
4 4
0 1
0 2
1 3
2 3
An undirected graph to the above input is shown below:
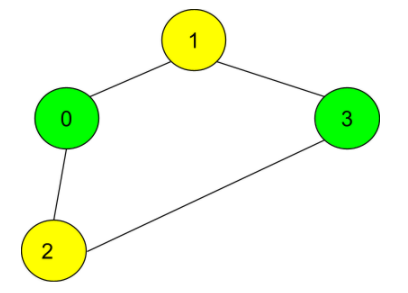
In the given input, the number of vertices is 4, and the number of edges is 4.
In the input, following the number of vertices and edges, a list of pairs of numbers is given where each pair (u, v) denotes an edge between vertex u and v.
As per the input, there is an edge between vertex 0 and vertex 1.
The vertices 0 and 2 have an edge between them.
The vertices 1 and 3 have an edge between them.
The vertices 2 and 3 have an edge between them.
As the graph can be colored using two colors, and no adjacent vertices share the same color, the graph is bipartite.
Problem approach
The idea is very simple. To separate the vertices of the graph in two sets such that no two vertices of a set are connected, we will try to color the vertices of the graph using two colors only.
If any of the adjacent vertices are of the same color, the graph is not bipartite. Else, it is bipartite.
04
Round
Medium
Face to Face
Duration60 minutes
Interview date22 Oct 2019
Coding problem1
This was more of a discussion round revolving around Cyber Security and Computer Networks. Interviewer was more interested in my approaches and the assumptions I am taking while solving the problem.
1. Computer Network Question
Design a mechanism such that there should not be any packet loss while transmitting the information over a network, and also to come up with a way, the credentials can be securely transmitted over a network.
Problem approach
Tip 1 : I came up with some of the hashing algorithms, and then he modified the input and I had to change my encryption algorithm accordingly.
Tip 2 : He wanted to understand how well I know the networking and the OSI model and how well can I diagonise the reasons for packet drop.

Here's your problem of the day
Solving this problem will increase your chance to get selected in this company
Skill covered: Programming
How do you remove whitespace from the start of a string?
Choose another skill to practice
Similar interview experiences
SDE - Intern
2 rounds | 4 problems
Interviewed by Arcesium
3738 views
0 comments
0 upvotes
SDE - Intern
2 rounds | 3 problems
Interviewed by Arcesium
1485 views
0 comments
0 upvotes
SDE - Intern
3 rounds | 5 problems
Interviewed by Arcesium
2682 views
0 comments
0 upvotes
SDE - Intern
2 rounds | 4 problems
Interviewed by Arcesium
1447 views
0 comments
0 upvotes
Companies with similar interview experiences
SDE - Intern
3 rounds | 5 problems
Interviewed by BNY Mellon
2347 views
0 comments
0 upvotes
SDE - Intern
4 rounds | 8 problems
Interviewed by NCR Corporation
2287 views
0 comments
0 upvotes
SDE - Intern
2 rounds | 4 problems
Interviewed by BNY Mellon
2107 views
0 comments
0 upvotes