Introduction
The National Eligibility Test (NET) is conducted on behalf of the University Grants Commission (UGC) to determine the eligibility of Indian nationals for the Eligibility of Assistant Professorship, Junior Research Fellowship, or both for Indian Universities and Colleges. In this blog, we will go through the questions and solutions of June 2014 Paper-II of UGC - NET EXAM. In this blog, we have covered from question 1 to question 25. The remaining questions are covered in June 2014 Paper II Part-2.
Questions
- Infrared signals can be used for short-range communication in a closed area using _______ propagation.
(A) ground (B) sky (C) line of sight (D) space
ANS - (C)
Solution - Infrared signals can be used for short-range communication in a closed area using Line of sight propagation. Infrared with range 300 GHz onwards lies in EHF and belongs to the Line of sight.
2. A bridge has access to the _______ address in the same network.
(A) Physical (B) Network (C) Datalink (D) Application
ANS - (A)
Solution - A bridge operates at the data link layer, giving access to all stations' physical addresses.
3. The minimum frame length for 10 Mbps Ethernet is _______ bytes and the maximum is _______ bytes.
(A) 64 & 128 (B) 128 & 1518 (C) 1518 & 3036 (D) 64 & 1518
ANS - (D)
Solution - The minimum size of an Ethernet frame is 64 bytes.
4. The bit rate of a signal is 3000 bps. If each signal unit carries 6 bits, the baud rate of the signal is _______.
(A) 500 baud/sec (B) 1000 baud/sec (C) 3000 baud/sec (D) 18000 baud/sec.
ANS - (A)
Solution - baud rate= bitrate/No. of bits in each signal = 3000/6= 500 bauds/sec.
5. Match the following :
List – I List – II a. Physical layer i. Allow resources to network access b. Datalink layer ii. Move packets from one destination to other c. Network layer iii. The process to process message delivery d. Transport layer iv. Transmission of bitstream e. Application Layer v. Formation of frames Codes :
a b c d e
(A) iv v ii iii i
(B) v iv i ii iii
(C) i iii ii v iv
(D) i ii iv iii v
ANS - (A)
Solution -
Physical Layer:: responsible for Transmission of the packet in the stream of bit with a proper encoding method.
Data Link Layer:: Formation of the frame means framing is done at this layer and max frame size 1500B.
Network Layer:: Door to Door delivery of datagram(Packet.)
Transport Layer:: End-to-end delivery.
6. A grammar G is LL(1) if and only if the following conditions hold for two distinct productions A → α | β I. First, (α) ∩ First (β) ≠ {a} where a is some terminal symbol of the grammar. II. First (α) ∩ First (β) ≠ λ III. First (α) ∩ Follow
(A) = φ if λ ∈ First (β) (A) I and II (B) I and III (C) II and III (D) I, II and III
ANS - (D)
Solution - For a grammar to be LL(1), each production must be unique. The following conditions must hold:-
First(α)∩First(β)=ϕ
Hence I and II are true.
If either α or β (not both) derive ϵ, then
First(<remaining>)∩Follow(A)=ϕ
7. Which of the following suffices to convert an arbitrary CFG to an LL(1) grammar?
(A) Removing left recursion alone (B) Removing the grammar alone (C) Removing left recursion and factoring the grammar (D) None of the above
ANS - (D)
Solution - Removing left recursion and factoring the grammar do not suffice to convert an arbitrary CFG to LL(1) grammar.
8. A shift-reduce parser suffers from
(A) shift-reduce conflict only (B) reduce reduce conflict only (C) both shift-reduce conflict and reduce reduce conflict (D) shift handle and reduce handle conflicts
ANS - (C)
Solution - A shift-reduce parser scans and parses the input text in one forward pass over the text without backing up.
9. The context free grammar for the language L = {an b mc k | k = |n – m|, n > 0, m > 0, k > 0} is
(A) S → S1 S3 , S1 → aS1 c | S2 | λ, S2 → aS2 b|λ, S3 → aS3 b| S4 | λ, S4 → bS4 c|λ
(B) S → S1 S3 , S1→ aS1 S2 c | λ, S2 → aS2 b|λ, S3 → aS3 b| S4 |λ, S4 → bS4 c|λ (C) S → S1 |S2 , S1→ aS1 S2 c | λ, S2 → aS2 b | λ, S3 → aS3 b | S4 |λ, S4 → bS4 c|λ
(D) S → S1 | S3 , S1→ aS1 c|S2 | λ, S2 → aS2 b | λ, S3 → a S3 b| S4 | λ, S4 → bS4 c | λ
ANS - (D)
Solution -
Option D is correct as first part has #a = #b+#c and second part has #b = #a+#c, which is required for given language.
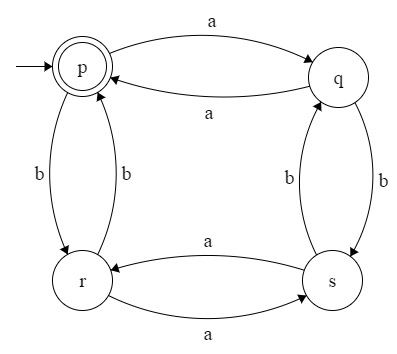
10. The regular grammar for the language L = {w|na (w) and nb (w) are both even, w ∈ {a, b}*} is given by : (Assume, p, q, r and s are states)
(A) p → aq | br | λ, q → bs | ap r → as | bp, s → ar | bq, p, and s are initial and final states.
(B) p → aq | br, q → bs | ap r → as | bp, s → ar | bq, p, and s are initial and final states.
(C) p → aq | br | λ, q → bs | ap r → as | bp, s → ar | bq p is both initial and final states.
(D) p → aq | br, q → bs | ap r → as | bp, s → ar | bq p is both initial and final states.
ANS - (C)
Solution -
This is Even-Even Language. No of a's are divisible by 2, and No of b's are divisible by 2.
11. KPA in CMM stands for
(A) Key Process Area
(B) Key Product Area
(C) Key Principal Area
(D) Key Performance Area
ANS - (A)
Solution - KPA in CMM stands for Key Process Area.
12. Which one of the following is not a risk management technique for managing the risk due to unrealistic schedules and budgets?
(A) Detailed multi-source cost and schedule estimation.
(B) Design cost
(C) Incremental development
(D) Information hiding
ANS - (D)
Solution - Risk management is the process of identifying, assessing, and controlling threats to an organization's capital and earnings. Risk management can be considered dealing with the possibility and actual occurrence of those events that are not regular or commonly expected. Information Hiding is not a Risk Management Technique because Information hiding is the principle of segregation of the design decisions in a computer program that are most likely to change, thus protecting other parts of the program from extensive modification if the design decision is changed. Information hiding is a powerful programming technique because it reduces complexity.
13. _______ of a system is the structure or structures of the system which comprise software elements, the externally visible properties of these elements, and the relationship amongst them.
(A) Software construction
(B) Software evolution
(C) Software architecture
(D) Software reuse
ANS - (C)
Solution - The software architecture of a program or a computing system is the structure or structures of the system, which comprise software components, the externally visible properties of those components, and the relationships among them.
14. In function point analysis, the number of complexity adjustment factors is
(A) 10 (B) 12 (C) 14 (D) 20
ANS - (C)
Solution - There are 14 complexity adjustment factors, listed below:-
1. Requirement for reliable backup and recovery
2. Requirement for data communication
3. Extent of distributed processing
4. Performance requirements
5. Expected operational environment
6. Extent of online data entries
7 Extent of multi-screen or multi-operation online data input.
8. Extent of online updating of master files
9. Extent of complex inputs, outputs, online queries, and files
10. Extent of complex data processing
11. Extent that currently developed code can be designed for reuse
12. Extent of conversion and installation included in the design
13. Extent of multiple installations in an organization and variety of customer organizations
14. Extent of change and focus on ease of use
15. Regression testing is primarily related to
(A) Functional testing
(B) Development testing
(C) Data flow testing
(D) Maintenance testing
ANS - (D)
Solution - Regression testing is the process of testing changes to computer programs to make sure that the older programming still works with the new changes.so it has to be related to Maintenance Testing.
16. How many different truth tables of the compound propositions are there that involve the propositions p & q?
(A) 2 (B) 4 (C) 8 (D) 16
ANS - (D)
Solution - There are 2 variables p and q formula is 2^2^n, so the answer is 16.
17. A Boolean function F is called self-dual if and only if F(x1, x2, … xn ) = F(– x1, – x2, … – xn ) How many Boolean functions of degree n are self-dual?
(A) 2n (B) (2)2 n (C) (2) n 2 (D) (2) 2n–1
ANS - (D)
Solution - A function is self-dual if F = FD. A boolean function with n variables is self-dual if it is a neutral function and its terms are mutually exclusive.
number of mutually exclusive pairs : 2n / 2 -> 2n-1
out of a pair, I have to select 1 term, so I have 2 choices.
18. Which of the following statement(s) is (are) not correct?
i. The 2's complement of 0 is 0. ii. In 2's complement, the left-most bit cannot be used to express a quantity. iii. For an n-bit word (2's complement) which includes the sign bit, there are 2n–1 positive integer, 2n+1 negative integers, and one 0 for a total of 2n unique states. iv. In 2's complement, the significant information is contained in the 1's of positive numbers and 0's of the negative numbers.
(A) i & iv (B) i & ii (C) iii (D) iv
ANS - (C)
Solution - 3 bits, one zero∙
total 2^3 unique states,
2^n-1 positive numbers=2^3-1=4 positive numbers. But there are 2n+1 negative numbers. Hence incorrect.
19. The notation ∃!XP(x) denotes the proposition "there exists a unique x such that P(x) is true." Give the truth values of the following statements: I. ∃!XP(x) → ∃XP(x) II. ∃!x ¬ P(x) → ¬∀xP(x)
(A) Both I & II are true. (B) Both I & II are false. (C) I – false, II – true (D), I – true, II – false
ANS - (A)
Solution -
I: If there is a unique x with P(x) true, then there is an x with P(x) true. This is TRUE as exactly 1 is a subset of at least one.
II: If there exists a unique x with P(x) false, then there does not exist an x with P(x) true. This is FALSE (contradiction) as all except one x can have P(x) true.
20. Give a compound proposition involving propositions p, q, and r that is true when exactly two of p, q, and r are true and is false otherwise.
(A) (p∨q∧¬r) ∧ (p∧¬q∧r) ∧ (¬p∧q∧r)
(B) (p∧q∧¬r) ∧ (p∨q∧¬r) ∧ (¬p∧q∧r)
(C) (p∧q∧¬r) ∨ (p∧¬q∧r) ∧ (¬p∧q∧r)
(D) (p∧q∧¬r) ∨ (p∧¬q∧r) ∨ (¬p∧q∧r)
ANS - (D)
Solution - The compound proposition involving propositions p, q, and r which is true when exactly two of p, q, and r are true and is false otherwise is (p∧q∧¬r) ∨ (p∧¬q∧r) ∨ (¬p∧q∧r) as option D is true in all cases.
21. Consider the graph given below: Which one of the following graphs is isomorphic to the above graph?
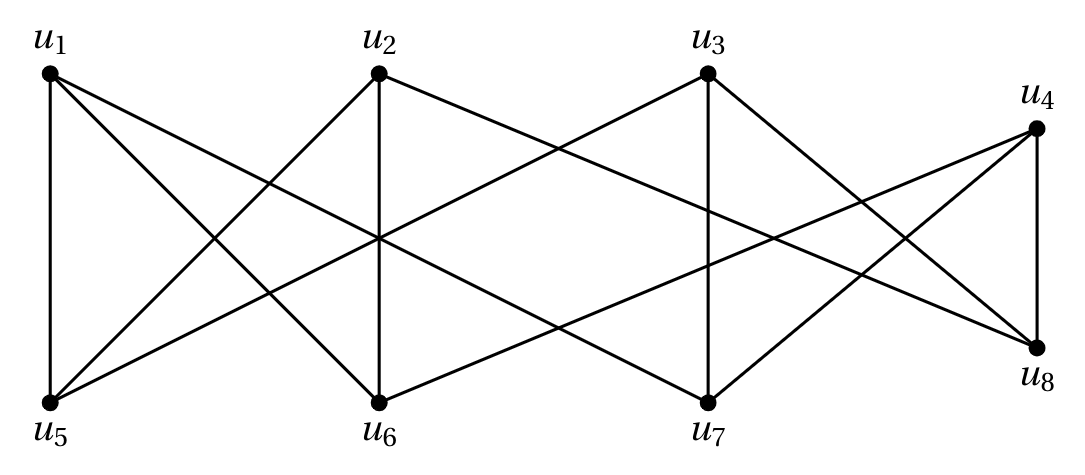
(A) 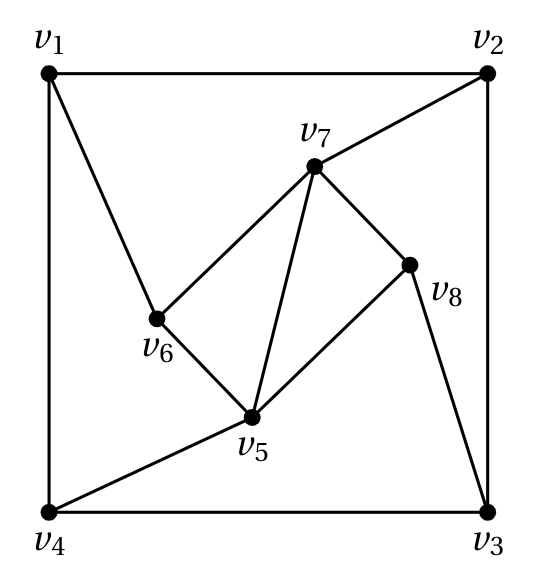
(B) 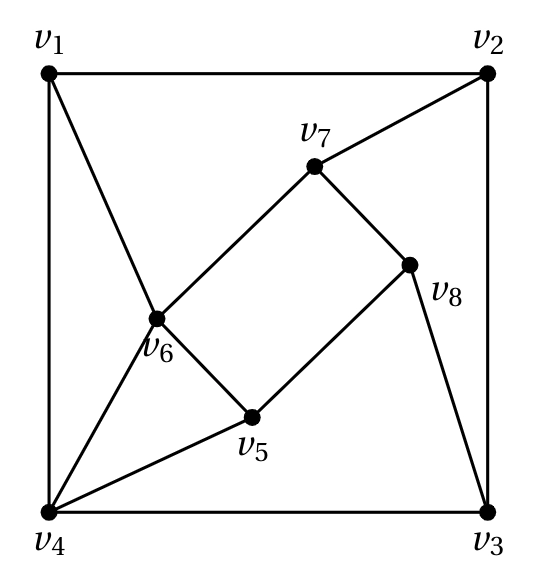
(C) 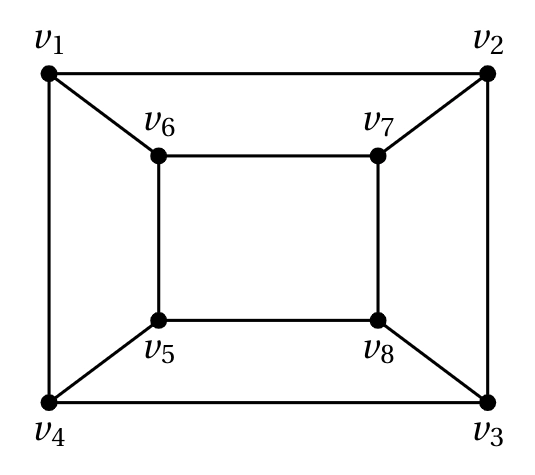
(D) 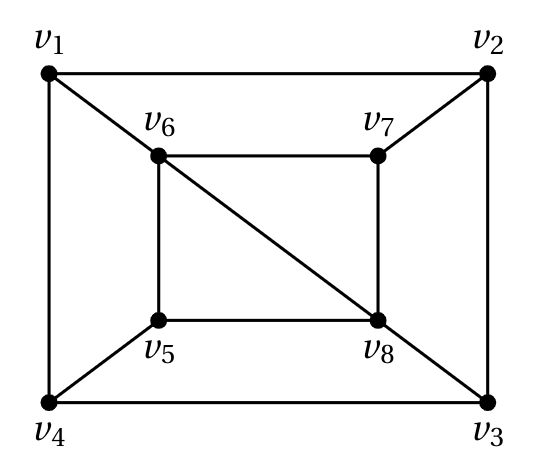
ANS - (C)
Solution - From the given figure we can say that every vertex has a degree = 3,
in all options but in C, the graph has at least one vertex with degree = 4. So option C is the correct answer.
22. The upper bound and lower bound for the number of leaves in a B-tree of degree K with height h is given by :
(A) Kh and 2 K / 2 h–1
(B) K*h and 2 K / 2 h–1
(C) Kh and 2 K / 2 h–1
(D) K*h and 2 K / 2 h–1
ANS - (A)
Solution - The upper bound and lower bound for the number of leaves in a B-tree of degree K with height h is given by Kh and 2 K / 2 h–1.
23. Consider a complete bipartite graph km,n. For which values of m and n does this, complete graph have a Hamilton circuit
(A) m = 3, n = 2
(B) m = 2, n = 3
(C) m = n > 2
(D) m = n > 3
ANS - (C)
Solution - Km,n has a Hamilton circuit if and only if m=n>2
24. Big-O estimates for the factorial function and the logarithm of the factorial function i.e. n! and log n! is given by
(A) O(n!) and O(n log n)
(B) O(nn ) and O(n log n)
(C) O(n!) and O(log n!)
(D) O(nn ) and O(log n!)
ANS - (B)
Solution - n!=1*2*3*4............*n-1*n <= n*n*n*n..........*n=(n)n =O((n)n)
log(n!)<=log(n)n =n log n=O(n log n)
25. How many cards must be chosen from a deck to guarantee that at least i. two aces of two kinds are chosen. ii. two aces are chosen. iii. two cards of the same kind are chosen. iv. two cards of two different kinds are chosen.
(A) 50, 50, 14, 5 (B) 51, 51, 15, 7 (C) 52, 52, 14, 5 (D) 51, 51, 14, 5
ANS - (A)
Solution - since we have to be sure (guarantee) to consider the worst cases for all
i)two aces of the same kind are chosen (first 48 cards without an ace 49th will surely be an ace and 50th will be of another ace) Here kind word is incorrectly given
ii) two aces are chosen first 48 cards can be without an ace then the 49th and 50th will definitely be aces.
iii)two cards of the same kind that is the same number so the first 13 can be of different numbers but the 14th will definitely match with someone
iv)2 cards of 2 different kinds let the first 4 are of the same number say all ace or all 2 etc now 5th one will be definitely a different number
So the answer is A 50 50 14 5.





