Working Of IDS
IDS first works on data collection and analyzing patterns. After data collection, IDS observes network traffic and matches the traffic patterns to known attacks. Once suspicious activity is detected, IDS sends an alarm to the administrator. IDS alarm helps the user/system troubleshoot the root sources of the issue.
Source: tenor
Intrusion Detection System uses two main intrusion detection methods:
- Signature-based intrusion detection
- Anomaly-based intrusion detection
Note: To learn about the detection method of IDS, you can refer to IDS Detection Methods.
Types of Intrusion Detection Systems
Intrusion detection systems are of the following types:
Host-Based Intrusion Detection System(HIDS)
Host-Based Intrusion Detection System or Host Intrusion Detection System runs on independent hosts or devices of the network. It examines events on a computer on the host computer rather than the traffic that passes around the system. It works by looking at data present in admin files on the computer. Admin files include log files and config files.
HIDS will back up all the configuration files so that settings can be restored in case some malicious program alters them. To monitor these changes, HIDS takes a screenshot of admin files from time to time and compares these changes. If the admin files were edited, deleted, or altered, an alert is sent to the administrator. Later these changes can be restored with the help of the previous screenshots. However, it won't block these changes; it only helps to alter if any unauthorized access occurs.
Network-Based Intrusion Detection System(NIDS)
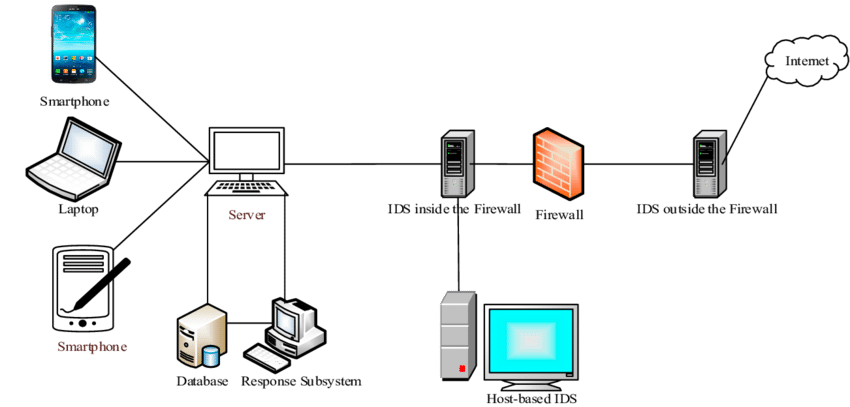
Network-Based Intrusion Detection System or Network Intrusion Detection System helps to examine traffic on your network from all devices on the network. Once any malicious activity is detected, an alert is sent to the administrator. To detect this traffic and analyze a network, NIDS includes a packet sniffer. NIDS performs an overall observation of passing traffic on the entire subnet once an abnormal behavior is detected, the alert is raised. An example of NIDS is installing it on a subnet where the firewall is present, to detect breaches in the firewall.
Protocol-based Intrusion Detection System(PIDS)
Protocol-based IDS consists of a system or agent that consistently resides on a web server, controlling and interpreting the protocols between device and server. A typical use of PIDS would be at the front end of the web server monitoring the protocols like HTTP or HTTPS stream. It can offer great protection because it understands HTTP and HTTPS relative to a web server. Similarly, a PIDS can be used to monitor many other protocols used by the computing system.
Application Protocol-based Intrusion Detection System(APIDS)
An Application Protocol-based Intrusion Detection System, also known as APIDS, is an intrusion detection system that monitors and analyzes a specific application protocol or protocols used by the computing system. It generally resides within a group of servers and identifies intrusions by monitoring and interpreting the communication on application-specific protocols. For example, it will monitor database protocols explicit to the middleware as it interacts with the database in the webserver.
Hybrid Intrusion Detection System
As the name suggests, a Hybrid intrusion detection system is made by combining two or more types of intrusion detection systems. In the hybrid approach, host agent or system data is combined with information to develop a complete network view. These systems are generally more effective than other intrusion detection systems.
Comparison of IDS with Firewalls
IDS and firewall both are related to network security, they protect your system from unauthorized access. The difference between firewalls and IDS lies in the scope of protection they are providing. The firewall protects the network from outside attacks, i.e., it looks for outward intrusions in order to stop them. It restricts access between networks to prevent intrusion. But if there is an attacker who is trying to breach the system from inside or any other inside intrusion, then the firewall won't signal. IDS looks for any suspected intrusion(both inside and outside the network), and once it happens, it will signal an alarm.
Examples of IDS
In today's time, various Intrusion Detection And Prevention Systems are widely used; since they are both 'detection and prevention' sytems, they are collectively termed as IDPS. Some examples of IDS are:
- SolarWinds Security Event Manager (SEM)
- McAfee
- Suricata
- Zeek
- Blumira
FAQs
-
Why is an Intrusion Detection System needed?
An intrusion detection system is needed because it enables users to detect and respond to malicious traffic, thus protecting them from Cyberattacks. It helps users to protect his system from outside and inside attacks.
-
Who is Misfeasor?
Misfeasor is a legitimate user who accesses or tries to access unauthorized data, programs, or resources. He is authorized for such access in some cases but misuses his privileges.
-
What is a firewall?
A Firewall is a network security device that monitors and filters incoming and outgoing network traffic based on a set of protocols.
-
What is an intrusion?
Intrusion can be defined as a breach in a network. It's unauthorized access by the attacker who doesn't have legitimate permission to access the network or system.
-
What is a packet sniffer?
A packet sniffer is hardware or software used to monitor network traffic. Sniffers work by examining streams of data packets that flow between computers on a network as well as between networked computers.
Key Takeaways
In this article, we have extensively discussed Intrusion Detection System, its classification, and its working. We also compared IDS with a Firewall. After all this discussion, we can say that IDS is the need of modern time that can ensure the protection of system or network from inside and outside intrusions.
We hope that this blog has helped you enhance your knowledge regarding Cyber Security and Intrusion Detection System, and if you would like to learn more, check out our articles, Cyber Security Principle, What is Cryptography, and Cyber attacks and their Types. Do upvote our blog to help other ninjas grow.
Happy Learning!