Introduction
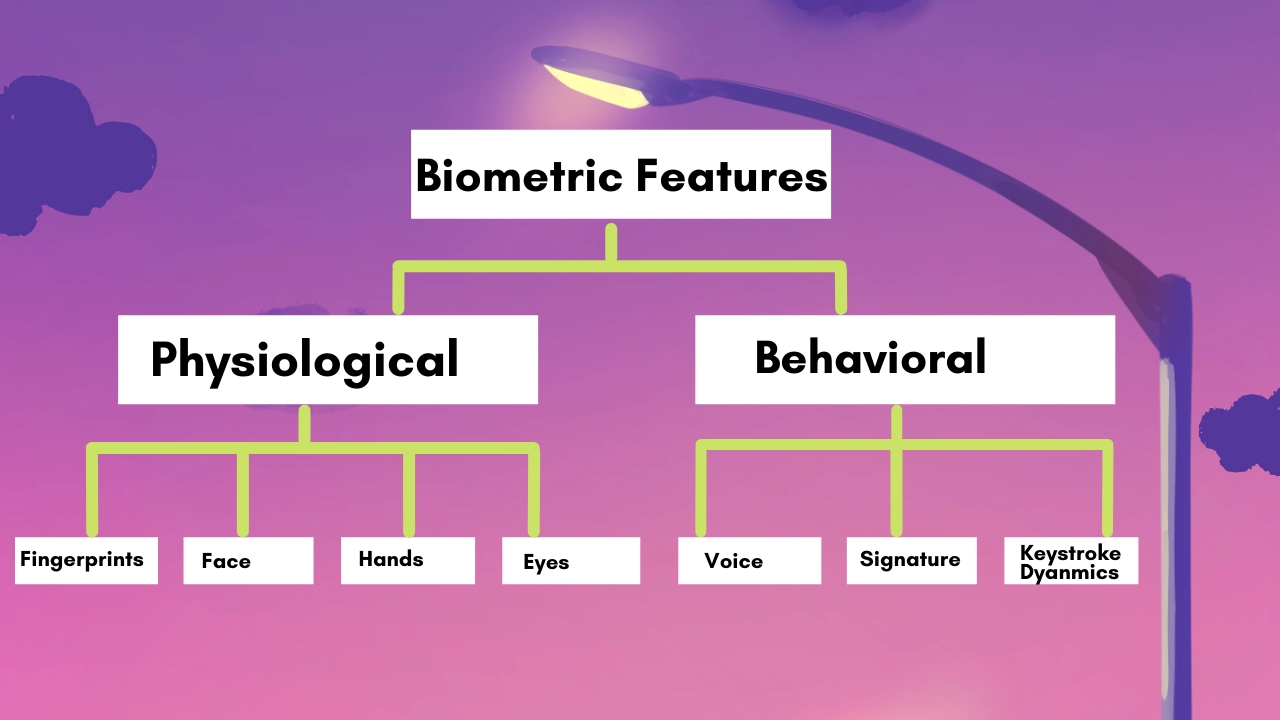
Biometric Systems are computer-assisted techniques of validating or detecting a live person's identification based on physiological traits such as a fingerprint or facial pattern or behavioural characteristics such as handwriting or keyboard patterns. The image below depicts some of the most commonly utilised biometric characteristics. Even if the latter may be easier to incorporate inside some specialised applications, a biometric system based on physiological parameters is more dependable than behavioural variables.
The only option to ensure the owner's presence during a transaction is to use biometric traits. Fingerprint-based solutions are successful in securing information and resources across a wide range of applications. The number of apps that use biometric technology to safeguard transactions is still somewhat restricted. On the one hand, certain hurdles are defined by people's lack of familiarity (and, in some cases, acceptance). Still, the expense of the requisite hardware/software and insufficient performance was arguably the most crucial factors for biometrics' underdevelopment in the past. Today's technology allows for the creation of low-cost systems with high performance that are suitable for a wide range of applications.
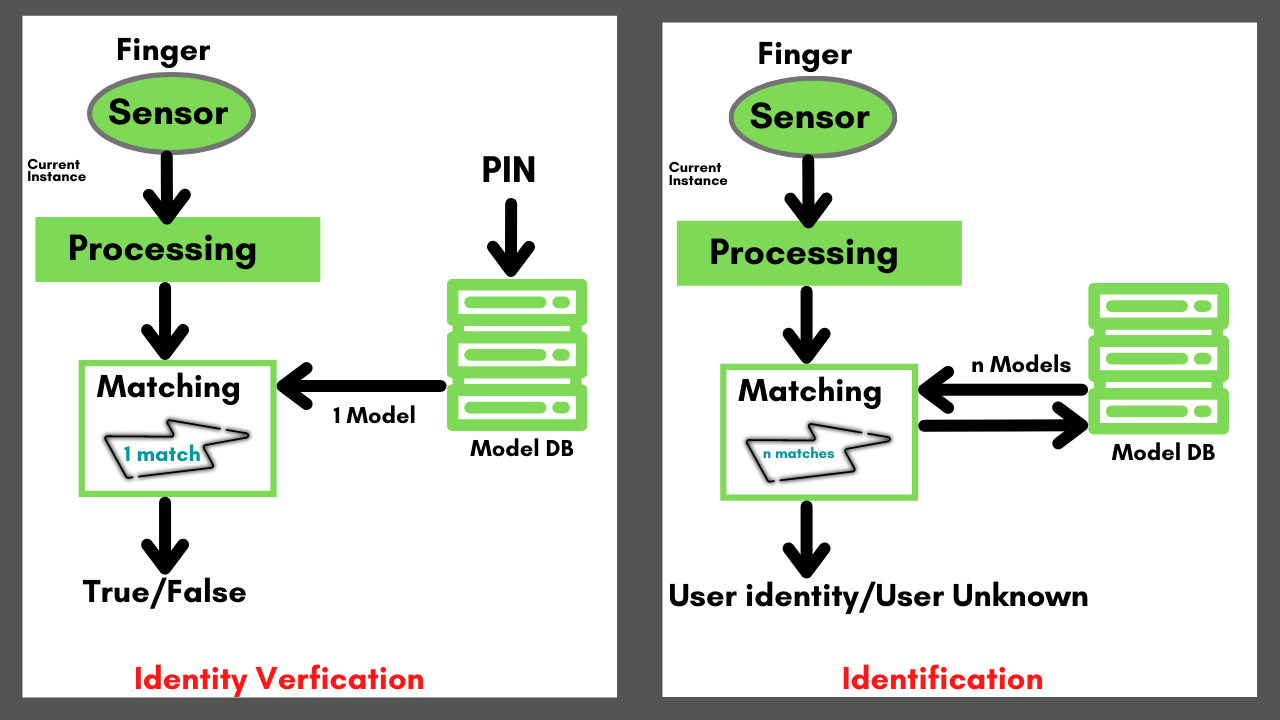
In the subject of biometric systems, there are two types of issues to consider:
- Identity verification (or simply verification) needs a person to declare their identity, for example, through the use of a PIN (Personal Identification Number); the system then compares (1:1) the person's current biometric characteristic to a previously obtained one retrieved via the PIN.
- The system must scan a list of candidates and determine if one fits the individual who needs to be identified. This is a more challenging operation because it necessitates a (1:N) match, which may be computationally expensive on massive databases.
All users must be enrolled before a biometric system will be utilised for verification or identification. During enrollment, the individual provides a sample of their biometric characteristic, which the system uses to create a compact model (or template) that summarises the discriminant characteristics. Models can be kept in a centralised database, disseminated across a network, or embedded in badges delivered to users, depending on the application. When an individual demands verification/identification, they provide a new sample of their fingerprint, which the system compares to the previously stored model(s).
Recommended Topic, 8085 Microprocessor Pin Diagram
The Architecture of Biometric System
Biometrics are automated techniques of determining a person's identity based on physiological and observable characteristics. Biometric technologies have changed the way people identify and verify themselves all across the world. Biometric methods measure different traits such as the face, fingerprints, handwriting, palmprints, hand geometry, gait, iris, retinal, and voice.
The following are the major components of a biometric system's architecture:
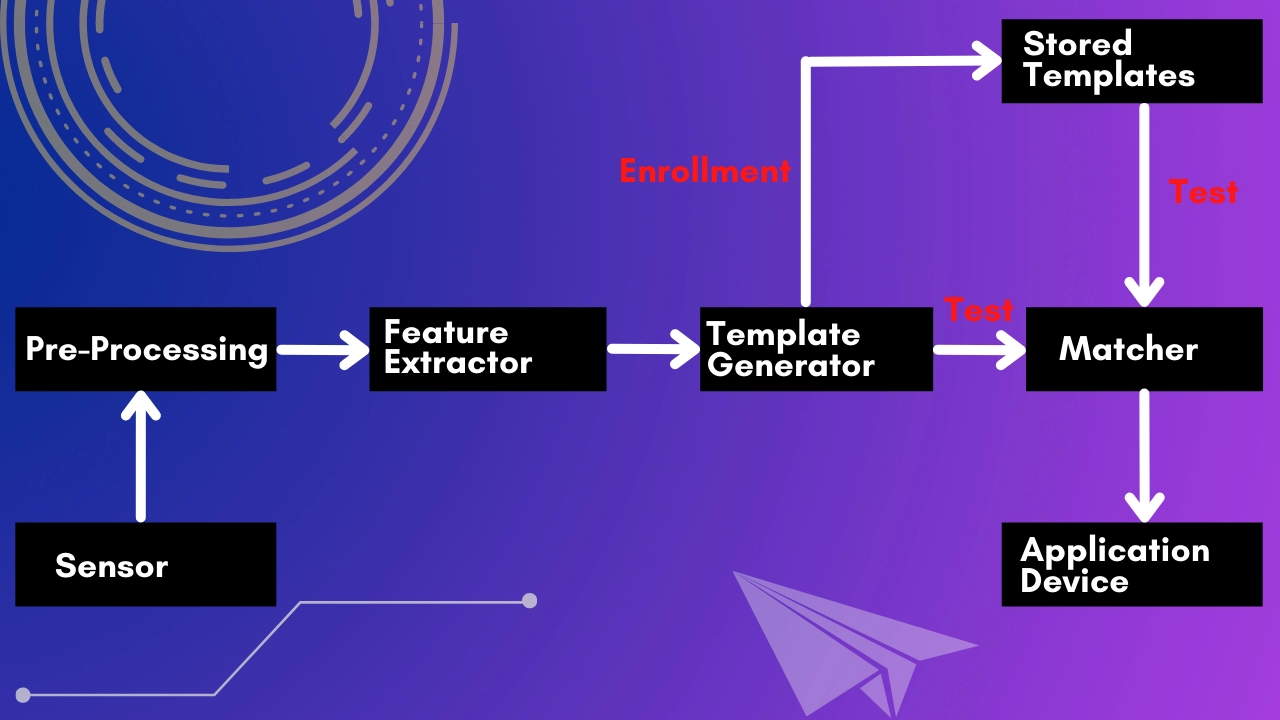
Sensor: The sensor is the initial component of a biometric system, and it collects all of the necessary biometric data. It serves as a link between the system and the outside world. Typically, it is an image capture system, but whether it has to be replaced or not depends on the features or qualities required.
Pre-processing: The second block is where all of the pre-processing takes place. Its purpose is to improve the input by removing sensor artefacts, background noise, and other factors. It normalises the data in some way.
Feature extractor: The third and most crucial phase in the biometric system is the feature extractor. Features must be extracted in order to be identified at a later stage. A feature extractor's purpose is to describe an item so that measurements may be used to recognise it.
Template generator: Using the extracted characteristics, the template generator creates the templates that are used for authentication. A template is a numeric vector or a picture divided into discrete tracts. The source groups' characteristics are combined to create a template. Templates are saved in the database for comparison purposes and as input for the match.
Matcher: A matcher is used to complete the matching step. The acquired template is provided to a matcher, who compares it to the stored templates using various methods like Hamming distance. The results will be generated when the inputs have been matched.
Application device: This is a gadget that employs biometric system results. Some examples of application devices are the iris recognition system and the facial recognition system.






